[Solved] Exercises Solidify Edge Complete Test Knowl Test Knowledge Chapter True False Mark T True Q37214689
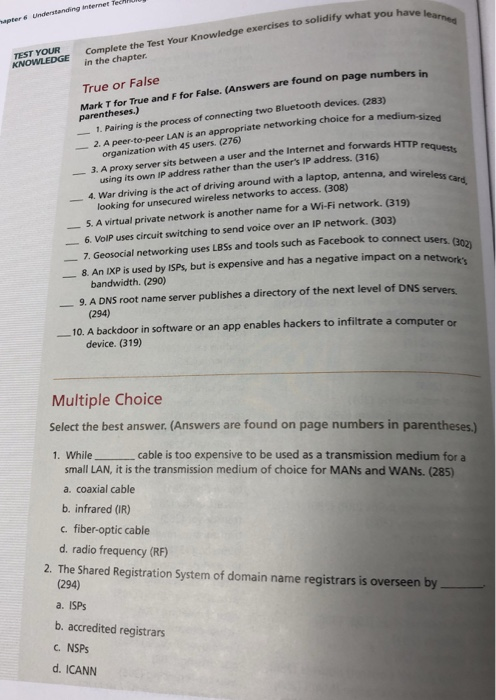
 exercises to solidify what you have edge YOUR Complete the Test Your Knowl TEST KNOWLEDGE in the chapter True or False Mark T for True and F for False. (Answers are found on page numbers in 1. Pairing is the process parentheses.) con s of connecting two Bluetooth devices. (283) 2. A peer-to-peer LAN is an appropriate networking choice for a medi organization with 45 users. (276) using its own IP address rather than the user’s IP address. (316) 4. War driving is the act of driving around with a laptop, antenna, and 3. A proxy server sits between a user and the Internet and forwards HTTP wireless card, looking for unsecured wireless networks to access. (308) 6. VoIP uses circuit switching to send voice over an IP network. (303) 7. Geosocial networking uses LBSs and tools such as Facebook to connect users bandwidth. (290) (294) device. (319) 5. A virtual private network is another name for a Wi-Fi network. (319) 8. An IXP is used by ISPs, but is expensive and has a negative impact on a 9. A DNS root name server publishes a directory of the next level of DNS servers 10. A backdoor in software or an app enables hackers to infiltrate a computer or Multiple Choice Select the best answer. (Answers are found on page numbers in parentheses.) 1. Whilecable is too expensive to be used as a transmission medium for a small LAN, it is the transmission medium of choice for MANs and WANs. (285) a. coaxial cable b. infrared (IR) c. fiber-optic cable d. radio frequency (RF) 2. The Shared Registration System of domain name registrars is overseen by (294) a. ISPs b. accredited registrars . NSPs d. ICANN ssions use radio to connect devices that are touching or nearby within 10 centimeters). (282) Radio frequency (RF) nfrared OR) e of the above d Non s of translating readable data into unreadable data to prevent process hauthorized access or use is called a decryption b. encryption c tunneling d private key is an intelligent connectivity device with one input port and one output s At that connects two network segments or two LANs. (286) a bridge b data switch c router d. gateway 6. А(n). – -, is a small packet that moves clockwise in a circle from node to node on a network. (281) a subnode b octet c. router d. token is when a hacker accesses a network to set up a fake website or send mail that looks like it is coming from an internal server. (308) a. War driving b. LAN jacking Spoofing d. Cracking 8. Large modern networks often are broken up intoor multiple groups of computers and devices that share a common function. (285) a. LANs b. segments c. VPNS d. servers 9. An IPv6 address includes8-bit numbers. (292) a. 8 b. 32 1,000,000 d. 128 324 Chapter Understanding internet Technologies and Security 10. Ais a kind of virus that spreads across a network, such as the Internet, b replicating itself. (311) a. Trojan horse b. worm c. backdoor d. DDoS Show transcribed image text exercises to solidify what you have edge YOUR Complete the Test Your Knowl TEST KNOWLEDGE in the chapter True or False Mark T for True and F for False. (Answers are found on page numbers in 1. Pairing is the process parentheses.) con s of connecting two Bluetooth devices. (283) 2. A peer-to-peer LAN is an appropriate networking choice for a medi organization with 45 users. (276) using its own IP address rather than the user’s IP address. (316) 4. War driving is the act of driving around with a laptop, antenna, and 3. A proxy server sits between a user and the Internet and forwards HTTP wireless card, looking for unsecured wireless networks to access. (308) 6. VoIP uses circuit switching to send voice over an IP network. (303) 7. Geosocial networking uses LBSs and tools such as Facebook to connect users bandwidth. (290) (294) device. (319) 5. A virtual private network is another name for a Wi-Fi network. (319) 8. An IXP is used by ISPs, but is expensive and has a negative impact on a 9. A DNS root name server publishes a directory of the next level of DNS servers 10. A backdoor in software or an app enables hackers to infiltrate a computer or Multiple Choice Select the best answer. (Answers are found on page numbers in parentheses.) 1. Whilecable is too expensive to be used as a transmission medium for a small LAN, it is the transmission medium of choice for MANs and WANs. (285) a. coaxial cable b. infrared (IR) c. fiber-optic cable d. radio frequency (RF) 2. The Shared Registration System of domain name registrars is overseen by (294) a. ISPs b. accredited registrars . NSPs d. ICANN
exercises to solidify what you have edge YOUR Complete the Test Your Knowl TEST KNOWLEDGE in the chapter True or False Mark T for True and F for False. (Answers are found on page numbers in 1. Pairing is the process parentheses.) con s of connecting two Bluetooth devices. (283) 2. A peer-to-peer LAN is an appropriate networking choice for a medi organization with 45 users. (276) using its own IP address rather than the user’s IP address. (316) 4. War driving is the act of driving around with a laptop, antenna, and 3. A proxy server sits between a user and the Internet and forwards HTTP wireless card, looking for unsecured wireless networks to access. (308) 6. VoIP uses circuit switching to send voice over an IP network. (303) 7. Geosocial networking uses LBSs and tools such as Facebook to connect users bandwidth. (290) (294) device. (319) 5. A virtual private network is another name for a Wi-Fi network. (319) 8. An IXP is used by ISPs, but is expensive and has a negative impact on a 9. A DNS root name server publishes a directory of the next level of DNS servers 10. A backdoor in software or an app enables hackers to infiltrate a computer or Multiple Choice Select the best answer. (Answers are found on page numbers in parentheses.) 1. Whilecable is too expensive to be used as a transmission medium for a small LAN, it is the transmission medium of choice for MANs and WANs. (285) a. coaxial cable b. infrared (IR) c. fiber-optic cable d. radio frequency (RF) 2. The Shared Registration System of domain name registrars is overseen by (294) a. ISPs b. accredited registrars . NSPs d. ICANN ssions use radio to connect devices that are touching or nearby within 10 centimeters). (282) Radio frequency (RF) nfrared OR) e of the above d Non s of translating readable data into unreadable data to prevent process hauthorized access or use is called a decryption b. encryption c tunneling d private key is an intelligent connectivity device with one input port and one output s At that connects two network segments or two LANs. (286) a bridge b data switch c router d. gateway 6. А(n). – -, is a small packet that moves clockwise in a circle from node to node on a network. (281) a subnode b octet c. router d. token is when a hacker accesses a network to set up a fake website or send mail that looks like it is coming from an internal server. (308) a. War driving b. LAN jacking Spoofing d. Cracking 8. Large modern networks often are broken up intoor multiple groups of computers and devices that share a common function. (285) a. LANs b. segments c. VPNS d. servers 9. An IPv6 address includes8-bit numbers. (292) a. 8 b. 32 1,000,000 d. 128 324 Chapter Understanding internet Technologies and Security 10. Ais a kind of virus that spreads across a network, such as the Internet, b replicating itself. (311) a. Trojan horse b. worm c. backdoor d. DDoS Show transcribed image text exercises to solidify what you have edge YOUR Complete the Test Your Knowl TEST KNOWLEDGE in the chapter True or False Mark T for True and F for False. (Answers are found on page numbers in 1. Pairing is the process parentheses.) con s of connecting two Bluetooth devices. (283) 2. A peer-to-peer LAN is an appropriate networking choice for a medi organization with 45 users. (276) using its own IP address rather than the user’s IP address. (316) 4. War driving is the act of driving around with a laptop, antenna, and 3. A proxy server sits between a user and the Internet and forwards HTTP wireless card, looking for unsecured wireless networks to access. (308) 6. VoIP uses circuit switching to send voice over an IP network. (303) 7. Geosocial networking uses LBSs and tools such as Facebook to connect users bandwidth. (290) (294) device. (319) 5. A virtual private network is another name for a Wi-Fi network. (319) 8. An IXP is used by ISPs, but is expensive and has a negative impact on a 9. A DNS root name server publishes a directory of the next level of DNS servers 10. A backdoor in software or an app enables hackers to infiltrate a computer or Multiple Choice Select the best answer. (Answers are found on page numbers in parentheses.) 1. Whilecable is too expensive to be used as a transmission medium for a small LAN, it is the transmission medium of choice for MANs and WANs. (285) a. coaxial cable b. infrared (IR) c. fiber-optic cable d. radio frequency (RF) 2. The Shared Registration System of domain name registrars is overseen by (294) a. ISPs b. accredited registrars . NSPs d. ICANN
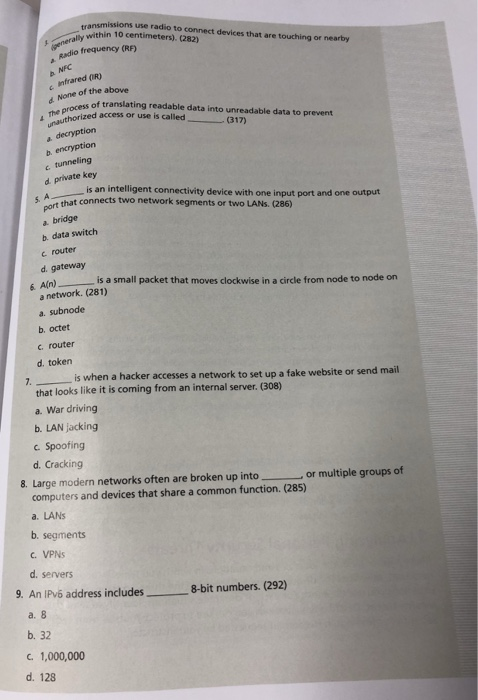
ssions use radio to connect devices that are touching or nearby within 10 centimeters). (282) Radio frequency (RF) nfrared OR) e of the above d Non s of translating readable data into unreadable data to prevent process hauthorized access or use is called a decryption b. encryption c tunneling d private key is an intelligent connectivity device with one input port and one output s At that connects two network segments or two LANs. (286) a bridge b data switch c router d. gateway 6. А(n). – -, is a small packet that moves clockwise in a circle from node to node on a network. (281) a subnode b octet c. router d. token is when a hacker accesses a network to set up a fake website or send mail that looks like it is coming from an internal server. (308) a. War driving b. LAN jacking Spoofing d. Cracking 8. Large modern networks often are broken up intoor multiple groups of computers and devices that share a common function. (285) a. LANs b. segments c. VPNS d. servers 9. An IPv6 address includes8-bit numbers. (292) a. 8 b. 32 1,000,000 d. 128
324 Chapter Understanding internet Technologies and Security 10. Ais a kind of virus that spreads across a network, such as the Internet, b replicating itself. (311) a. Trojan horse b. worm c. backdoor d. DDoS
Expert Answer
Answer to exercises to solidify what you have edge YOUR Complete the Test Your Knowl TEST KNOWLEDGE in the chapter True or False M… . . .
OR

