[Solved] 1 Name Define Least Five Malware Categories 2 Virus Signature Virus Signatures Used Identi Q37243990
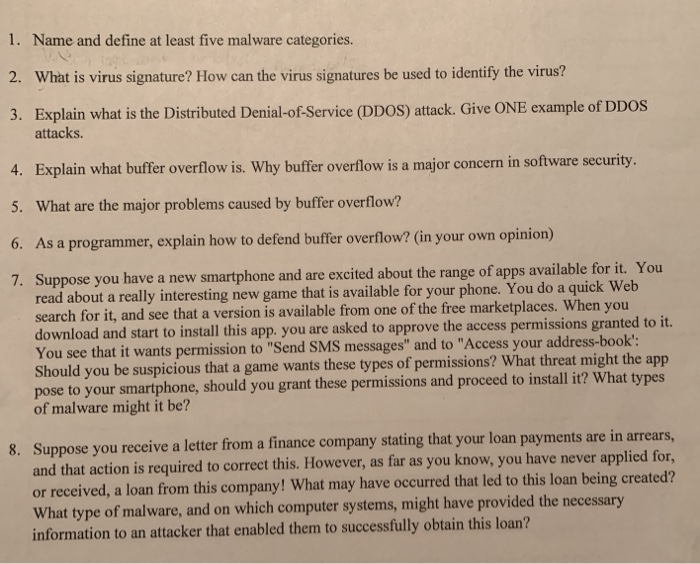 1. Name and define at least five malware categories. 2. What is virus signature? How can the virus signatures be used to identify the virus? 3. Explain what is the Distributed Denial-of-Service (DDoS) attack. Give ONE example of DDoS attacks. 4. Explain what buffer overflow is. Why buffer overflow is a major concern in software security 5. What are the major problems caused by buffer overflow? 6. As a programmer, explain how to defend buffer overflow? (in your own opinion) 7. Suppose you have a new smartphone and are excited about the range of apps available for it. You read about a really interesting new game that is available for your phone. You do a quick Web search for it, and see that a version is available from one of the free marketplaces. When you d start to install this app. you are asked to approve the access permissions granted to it. You see that it wants permission to “Send SMS messages” and to “Access your address-book: Should you be suspicious that a game wants these types of permissions? What threat might the app pose to your smartphone, of malware might it be? should you grant these permissions and proceed to install it? What types Suppose you receive a letter from a finance company stating that your loan payments are in arrears, 8. quired to correct this. However, as far as you know, you have never applied for, or received, a loan from this company! What may have occurred that led to this loan being created? What type of malware, and on which computer systems, might have provided the necessa information to an attacker that enabled them to successflly obtain this loan? Show transcribed image text 1. Name and define at least five malware categories. 2. What is virus signature? How can the virus signatures be used to identify the virus? 3. Explain what is the Distributed Denial-of-Service (DDoS) attack. Give ONE example of DDoS attacks. 4. Explain what buffer overflow is. Why buffer overflow is a major concern in software security 5. What are the major problems caused by buffer overflow? 6. As a programmer, explain how to defend buffer overflow? (in your own opinion) 7. Suppose you have a new smartphone and are excited about the range of apps available for it. You read about a really interesting new game that is available for your phone. You do a quick Web search for it, and see that a version is available from one of the free marketplaces. When you d start to install this app. you are asked to approve the access permissions granted to it. You see that it wants permission to “Send SMS messages” and to “Access your address-book: Should you be suspicious that a game wants these types of permissions? What threat might the app pose to your smartphone, of malware might it be? should you grant these permissions and proceed to install it? What types Suppose you receive a letter from a finance company stating that your loan payments are in arrears, 8. quired to correct this. However, as far as you know, you have never applied for, or received, a loan from this company! What may have occurred that led to this loan being created? What type of malware, and on which computer systems, might have provided the necessa information to an attacker that enabled them to successflly obtain this loan?
1. Name and define at least five malware categories. 2. What is virus signature? How can the virus signatures be used to identify the virus? 3. Explain what is the Distributed Denial-of-Service (DDoS) attack. Give ONE example of DDoS attacks. 4. Explain what buffer overflow is. Why buffer overflow is a major concern in software security 5. What are the major problems caused by buffer overflow? 6. As a programmer, explain how to defend buffer overflow? (in your own opinion) 7. Suppose you have a new smartphone and are excited about the range of apps available for it. You read about a really interesting new game that is available for your phone. You do a quick Web search for it, and see that a version is available from one of the free marketplaces. When you d start to install this app. you are asked to approve the access permissions granted to it. You see that it wants permission to “Send SMS messages” and to “Access your address-book: Should you be suspicious that a game wants these types of permissions? What threat might the app pose to your smartphone, of malware might it be? should you grant these permissions and proceed to install it? What types Suppose you receive a letter from a finance company stating that your loan payments are in arrears, 8. quired to correct this. However, as far as you know, you have never applied for, or received, a loan from this company! What may have occurred that led to this loan being created? What type of malware, and on which computer systems, might have provided the necessa information to an attacker that enabled them to successflly obtain this loan? Show transcribed image text 1. Name and define at least five malware categories. 2. What is virus signature? How can the virus signatures be used to identify the virus? 3. Explain what is the Distributed Denial-of-Service (DDoS) attack. Give ONE example of DDoS attacks. 4. Explain what buffer overflow is. Why buffer overflow is a major concern in software security 5. What are the major problems caused by buffer overflow? 6. As a programmer, explain how to defend buffer overflow? (in your own opinion) 7. Suppose you have a new smartphone and are excited about the range of apps available for it. You read about a really interesting new game that is available for your phone. You do a quick Web search for it, and see that a version is available from one of the free marketplaces. When you d start to install this app. you are asked to approve the access permissions granted to it. You see that it wants permission to “Send SMS messages” and to “Access your address-book: Should you be suspicious that a game wants these types of permissions? What threat might the app pose to your smartphone, of malware might it be? should you grant these permissions and proceed to install it? What types Suppose you receive a letter from a finance company stating that your loan payments are in arrears, 8. quired to correct this. However, as far as you know, you have never applied for, or received, a loan from this company! What may have occurred that led to this loan being created? What type of malware, and on which computer systems, might have provided the necessa information to an attacker that enabled them to successflly obtain this loan?
Expert Answer
Answer to 1. Name and define at least five malware categories. 2. What is virus signature? How can the virus signatures be used to… . . .
OR

