[Solved]1 Consider Following Two Variations Maximum Flow Problem Given Flow Network Multiple Sourc Q37185397
1. Consider the following two variations of the maximum flowproblem.
(a) Given a flow network with multiple sources and multiplesinks, compute a maximum flow from the sources to the sinks (i.e.,a flow that maximizes the total amount of flow out of all thesources. Note that the flow must satisfy all the threeconstraints).
(b) Given a flow network in which the nodes as well as the edgeshave capacities (positive integers), compute a maximum flow from sto t that respects the node capacities as well (i.e., for everynode in the network, the total amount of flow out of the nodeshould be bounded above by the capacity of the node). Show, byreductions to the maximum flow problem, that the above two problemscan be solved in time O(n 3 ), where n is the number of nodes inthe network.
Expert Answer
Answer to 1. Consider the following two variations of the maximum flow problem. (a) Given a flow network with multiple sources and… . . .
[Solved]1 Consider Following Set Candidate 3 Itemsets 1 2 3 1 2 6 1 3 4 2 3 4 2 4 5 3 4 6 4 5 6 Co Q37159547
1. Consider the following set of candidate 3-itemsets: {1, 2,3}, {1, 2, 6}, {1, 3, 4}, {2, 3, 4}, {2, 4, 5}, {3, 4, 6}, {4, 5,6} Construct a hash tree for the above candidate 3-itemsets. Assumethe tree uses a hash function where all odd-numbered items arehashed to the left child of a node, while the even-numbered itemsare hashed to the right child. A candidate k-itemset is insertedinto the tree by hashing on each successive item in the candidateand then following the appropriate branch of the tree according tothe hash value. Once a leaf node is reached, the candidate isinserted based on one of the following conditions: Condition 1: Ifthe depth of the leaf node is equal to k (the root is assumed to beat depth 0), then the candidate is inserted regardless of thenumber of itemsets already stored at the node. Condition 2: If thedepth of the leaf node is less than k, then the candidate can beinserted as long as the number of itemsets stored at the node isless than maxsize. Assume maxsize = 2 for this question. Condition3: If the depth of the leaf node is less than k and the number ofitemsets stored at the node is equal to maxsize, then the leaf nodeis converted into an internal node. New leaf nodes are created aschildren of the old leaf node. Candidate itemsets previously storedin the old leaf node are distributed to the children based on theirhash values. The new candidate is also hashed to its appropriateleaf node. How many leaf nodes are there in the candidate hashtree? How many internal nodes are there? Consider a transactionthat contains the following items: {1, 2, 3, 5, 6}. Using the hashtree constructed in part (a), which leaf nodes will be checkedagainst the transaction? What are the candidate 3-itemsetscontained in the transaction?
Expert Answer
Answer to 1. Consider the following set of candidate 3-itemsets: {1, 2, 3}, {1, 2, 6}, {1, 3, 4}, {2, 3, 4}, {2, 4, 5}, {3, 4, 6},… . . .
[Solved]1 Consider Inserting Data Integer Keys 22 14 12 48 36 12 Order Hash Table Size 11 Hashing Q37237370
Expert Answer
Answer to 1. Consider inserting data with integer keys 22, 14, 12, 48, 36, 12 in that order into a hash table of size 11 where the… . . .
[Solved]1 Consider Inserting Data Integer Keys 22 14 12 48 36 12 Order Hash Table Size 11 Hashing Q37210557
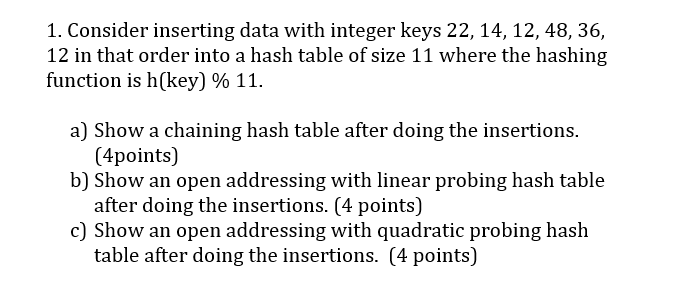
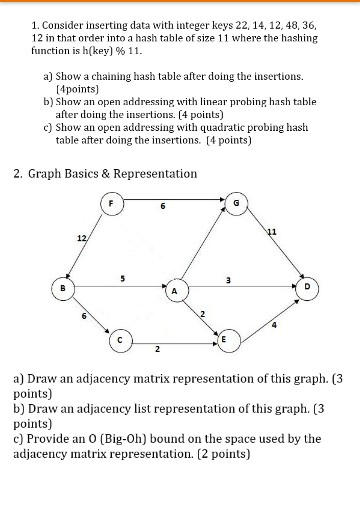
1. Consider inserting data with integer keys 22, 14,12, 48, 36, 12 in that order into a hash table of size 11 where the hashing function is h(key) % 11. a) Show a chaining hash table after doing the insertions. b) Show an open addressing with linear probing hash table c) Show an open addressing with quadratic probing hash (4points) after doing the insertions. (4 points) table after doing the insertions. (4 points) 2. Graph Basics & Representation ti 12 2 6 4 a) Draw an adjacency matrix representation of this graph. (3 points) b) Draw an adjacency list representation of this graph. (,3 points) c) Provide an O (Big-0h) bound on the space used by the adjacency matrix representation. (2 points) Show transcribed image text 1. Consider inserting data with integer keys 22, 14,12, 48, 36, 12 in that order into a hash table of size 11 where the hashing function is h(key) % 11. a) Show a chaining hash table after doing the insertions. b) Show an open addressing with linear probing hash table c) Show an open addressing with quadratic probing hash (4points) after doing the insertions. (4 points) table after doing the insertions. (4 points)
2. Graph Basics & Representation ti 12 2 6 4 a) Draw an adjacency matrix representation of this graph. (3 points) b) Draw an adjacency list representation of this graph. (,3 points) c) Provide an O (Big-0h) bound on the space used by the adjacency matrix representation. (2 points)
Expert Answer
Answer to 1. Consider inserting data with integer keys 22, 14,12, 48, 36, 12 in that order into a hash table of size 11 where the … . . .
[Solved]1 Consider Marie Program Hex Address 100 Label Start Hexadecimal Code Instruction Instruc Q37258275
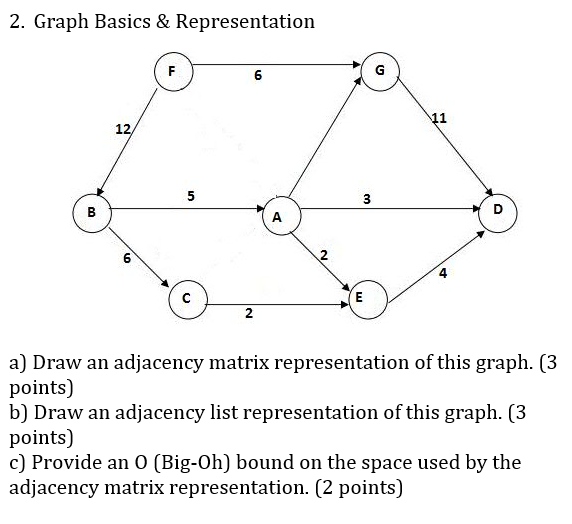
 questions 1&21. Consider the MARIE program below. Hex Address 100 Label Start, Hexadecimal code for each instruction Instruction LOAD X ADD Y SUBT Z STORE W CLEAR LOAD Y ADD W STORE W HALT HEX OOFF DEC 15 HEX 0010 HEX 0000 Load X- 101 102 103 104 105 106 107 108 Crear x, Y, z, 109 10A Halt 10B 10C SHmboly Address Draw the symbol table a. O A 1晗 b. What is the value store in the AC, X, Y, Z, W when’the program terminates. Write the following code segment in MARIE’s assembly language. If X = = Y then 2. Load X Locd Y Mw ltiplyTwo else Loud X Show transcribed image text 1. Consider the MARIE program below. Hex Address 100 Label Start, Hexadecimal code for each instruction Instruction LOAD X ADD Y SUBT Z STORE W CLEAR LOAD Y ADD W STORE W HALT HEX OOFF DEC 15 HEX 0010 HEX 0000 Load X- 101 102 103 104 105 106 107 108 Crear x, Y, z, 109 10A Halt 10B 10C SHmboly Address Draw the symbol table a. O A 1晗 b. What is the value store in the AC, X, Y, Z, W when’the program terminates. Write the following code segment in MARIE’s assembly language. If X = = Y then 2. Load X Locd Y Mw ltiplyTwo else Loud X
questions 1&21. Consider the MARIE program below. Hex Address 100 Label Start, Hexadecimal code for each instruction Instruction LOAD X ADD Y SUBT Z STORE W CLEAR LOAD Y ADD W STORE W HALT HEX OOFF DEC 15 HEX 0010 HEX 0000 Load X- 101 102 103 104 105 106 107 108 Crear x, Y, z, 109 10A Halt 10B 10C SHmboly Address Draw the symbol table a. O A 1晗 b. What is the value store in the AC, X, Y, Z, W when’the program terminates. Write the following code segment in MARIE’s assembly language. If X = = Y then 2. Load X Locd Y Mw ltiplyTwo else Loud X Show transcribed image text 1. Consider the MARIE program below. Hex Address 100 Label Start, Hexadecimal code for each instruction Instruction LOAD X ADD Y SUBT Z STORE W CLEAR LOAD Y ADD W STORE W HALT HEX OOFF DEC 15 HEX 0010 HEX 0000 Load X- 101 102 103 104 105 106 107 108 Crear x, Y, z, 109 10A Halt 10B 10C SHmboly Address Draw the symbol table a. O A 1晗 b. What is the value store in the AC, X, Y, Z, W when’the program terminates. Write the following code segment in MARIE’s assembly language. If X = = Y then 2. Load X Locd Y Mw ltiplyTwo else Loud X
Expert Answer
Answer to 1. Consider the MARIE program below. Hex Address 100 Label Start, Hexadecimal code for each instruction Instruction LOAD… . . .
[Solved]1 Consider Model Cylinderical Hydraulic Reservoir Bottom Flow Valve Input Qin Output Param Q37224061
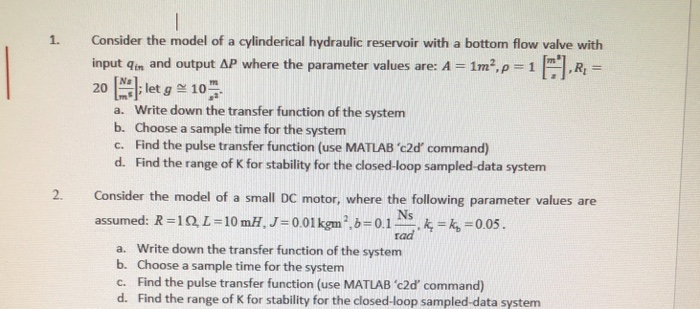 answer 1 and 2 please1. Consider the model of a cylinderical hydraulic reservoir with a bottom flow valve with input qin and output ΔΡ where the parameter values are: A-1m2,p-1 PI, RI 201 ; let g 10. Ns , a. Write down the transfer function of the system b. Choose a sample time for the system c. Find the pulse transfer function (use MATLAB’c2d command) d. Find the range of K for stability for the closed-loop sampled-data system 2. Consider the model of a small DC motor, where the following parameter values are assumed: R=IQL-10ml. J-0.01 kgm 2,6-0.1프’k-k,-0.05. rad a. Write down the transfer function of the system b. Choose a sample time for the system c. Find the pulse transfer function (use MATLAB ‘c2d’ command) d. Find the range of K for stability for the closed-loop sampled-data system Show transcribed image text 1. Consider the model of a cylinderical hydraulic reservoir with a bottom flow valve with input qin and output ΔΡ where the parameter values are: A-1m2,p-1 PI, RI 201 ; let g 10. Ns , a. Write down the transfer function of the system b. Choose a sample time for the system c. Find the pulse transfer function (use MATLAB’c2d command) d. Find the range of K for stability for the closed-loop sampled-data system 2. Consider the model of a small DC motor, where the following parameter values are assumed: R=IQL-10ml. J-0.01 kgm 2,6-0.1프’k-k,-0.05. rad a. Write down the transfer function of the system b. Choose a sample time for the system c. Find the pulse transfer function (use MATLAB ‘c2d’ command) d. Find the range of K for stability for the closed-loop sampled-data system
answer 1 and 2 please1. Consider the model of a cylinderical hydraulic reservoir with a bottom flow valve with input qin and output ΔΡ where the parameter values are: A-1m2,p-1 PI, RI 201 ; let g 10. Ns , a. Write down the transfer function of the system b. Choose a sample time for the system c. Find the pulse transfer function (use MATLAB’c2d command) d. Find the range of K for stability for the closed-loop sampled-data system 2. Consider the model of a small DC motor, where the following parameter values are assumed: R=IQL-10ml. J-0.01 kgm 2,6-0.1프’k-k,-0.05. rad a. Write down the transfer function of the system b. Choose a sample time for the system c. Find the pulse transfer function (use MATLAB ‘c2d’ command) d. Find the range of K for stability for the closed-loop sampled-data system Show transcribed image text 1. Consider the model of a cylinderical hydraulic reservoir with a bottom flow valve with input qin and output ΔΡ where the parameter values are: A-1m2,p-1 PI, RI 201 ; let g 10. Ns , a. Write down the transfer function of the system b. Choose a sample time for the system c. Find the pulse transfer function (use MATLAB’c2d command) d. Find the range of K for stability for the closed-loop sampled-data system 2. Consider the model of a small DC motor, where the following parameter values are assumed: R=IQL-10ml. J-0.01 kgm 2,6-0.1프’k-k,-0.05. rad a. Write down the transfer function of the system b. Choose a sample time for the system c. Find the pulse transfer function (use MATLAB ‘c2d’ command) d. Find the range of K for stability for the closed-loop sampled-data system
Expert Answer
Answer to 1. Consider the model of a cylinderical hydraulic reservoir with a bottom flow valve with input qin and output ΔΡ wher… . . .
[Solved]1 Consider Ranking Documents Using Binary Independence Model Bim Shown Rsva 2 Log O P Prob Q37185550
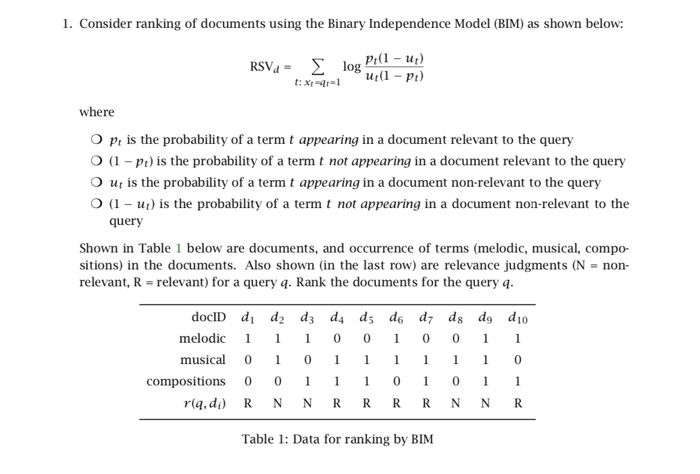
 1. Consider ranking of documents using the Binary Independence Model (BIM) as shown below: RSVa-2 log where O p is the probability of a term t appearing in a document relevant to the query O (1-p is the probability of a term t not appearing in a document relevant to the query O (1-u) is the probability of a term t not appearing in a document non-relevant to the Shown in Table 1 below are documents, and occurrence of terms (melodic, musical, compo- O ut is the probability of a term t appearing in a document non-relevant to the query query sitions) in the documents. Also shown (in the last row) are relevance judgments (N-non relevant, R relevant) for a query q. Rank the documents for the query q melodic 1 1 0 000 1 1 musical 001 1 0 0 10 1 compositions 0 0 riq,d) RN NRRRR NNR Table 1: Data for ranking by BIM 2. Consider ranking of documents using the Best Match 25 (BM25) algorithm as shown below: RSVd tfi.4 + k2 ti.q tfi.ą +k2 (rt +0.5)/(R – ri0.5) (dfi -ri 0.5)/(D -R dfi r0.5) log tfidki -b)+b idi-a-1 avgidl where O ki, k2, and b are empirically-set parameters. Typical values are: ki 리2,0 k2 s1000, and b-0.75. For this problem, use k2-100. o the number of relevant documents (in the collection) in which the term i occurs O dfi is the document frequency of the teri. That is, the number of documents (in the collection) in which the term i occurs O D is the total number of documents in the collection O R is the number of documents relevant to the query O tfia is the number of times the term i occurs in document d O tfi.4 is the number of times the term i occurs in the query q O dl is document length O avg(dl) average document length, which is the average length across all documents in the collection When no relevance information is given, R- 0. This is the case for this problem. Assume D- 50,000, the term information occurs in 40,000 documents in the collection, and the term retrieval occurs in 30,000 documents in the collection. Consider a document di in which the term information occurs 40 times, and the term retrieval occurs 30 times. Assume the ratio gidli 0.9). Consider the query of document length to average document length is 0.9 (i.e., avg(dl) 4-information retrieval. Calculate the RSV for (di)pair using the BM25 algorithm. 3. Consider ranking of documents using a Language Modeling-based IR algorithm. distinct term t in q where O tr.4 is the term frequency -number of occurrences of t in query a We estimate the parameters PitMa) using Maximum Likelihood Estimate (MLE) as: f,d where O Idl is the length of document d O tfr,d is the term frequency -number of occurrences of t in document d To avoid problem with zero probabilities, we smooth the estimates. First, we define where O Mc is the collection model O cfr is the number of occurrences of t in the collection O T = Σ1cfr is the total number of tokens in the collection We use Pt Mc) to smooth PtId) using Jelinek-Mercer smoothing as Let di The woman who opened fire at YouTube headquarters in Northern California may have been a disgruntled user of the video-sharing site, dz-Authorities are investigating a website that appears to show the same woman accusing YouTube of restricting her videos, and q YouTube fire. Rank di and d with respect to q using Jelinek-Mercer smoothing. Use λ-0.5 Clearly indicate any text normalization procedures performed on documents d1 and d2. Show transcribed image text 1. Consider ranking of documents using the Binary Independence Model (BIM) as shown below: RSVa-2 log where O p is the probability of a term t appearing in a document relevant to the query O (1-p is the probability of a term t not appearing in a document relevant to the query O (1-u) is the probability of a term t not appearing in a document non-relevant to the Shown in Table 1 below are documents, and occurrence of terms (melodic, musical, compo- O ut is the probability of a term t appearing in a document non-relevant to the query query sitions) in the documents. Also shown (in the last row) are relevance judgments (N-non relevant, R relevant) for a query q. Rank the documents for the query q melodic 1 1 0 000 1 1 musical 001 1 0 0 10 1 compositions 0 0 riq,d) RN NRRRR NNR Table 1: Data for ranking by BIM
1. Consider ranking of documents using the Binary Independence Model (BIM) as shown below: RSVa-2 log where O p is the probability of a term t appearing in a document relevant to the query O (1-p is the probability of a term t not appearing in a document relevant to the query O (1-u) is the probability of a term t not appearing in a document non-relevant to the Shown in Table 1 below are documents, and occurrence of terms (melodic, musical, compo- O ut is the probability of a term t appearing in a document non-relevant to the query query sitions) in the documents. Also shown (in the last row) are relevance judgments (N-non relevant, R relevant) for a query q. Rank the documents for the query q melodic 1 1 0 000 1 1 musical 001 1 0 0 10 1 compositions 0 0 riq,d) RN NRRRR NNR Table 1: Data for ranking by BIM 2. Consider ranking of documents using the Best Match 25 (BM25) algorithm as shown below: RSVd tfi.4 + k2 ti.q tfi.ą +k2 (rt +0.5)/(R – ri0.5) (dfi -ri 0.5)/(D -R dfi r0.5) log tfidki -b)+b idi-a-1 avgidl where O ki, k2, and b are empirically-set parameters. Typical values are: ki 리2,0 k2 s1000, and b-0.75. For this problem, use k2-100. o the number of relevant documents (in the collection) in which the term i occurs O dfi is the document frequency of the teri. That is, the number of documents (in the collection) in which the term i occurs O D is the total number of documents in the collection O R is the number of documents relevant to the query O tfia is the number of times the term i occurs in document d O tfi.4 is the number of times the term i occurs in the query q O dl is document length O avg(dl) average document length, which is the average length across all documents in the collection When no relevance information is given, R- 0. This is the case for this problem. Assume D- 50,000, the term information occurs in 40,000 documents in the collection, and the term retrieval occurs in 30,000 documents in the collection. Consider a document di in which the term information occurs 40 times, and the term retrieval occurs 30 times. Assume the ratio gidli 0.9). Consider the query of document length to average document length is 0.9 (i.e., avg(dl) 4-information retrieval. Calculate the RSV for (di)pair using the BM25 algorithm. 3. Consider ranking of documents using a Language Modeling-based IR algorithm. distinct term t in q where O tr.4 is the term frequency -number of occurrences of t in query a We estimate the parameters PitMa) using Maximum Likelihood Estimate (MLE) as: f,d where O Idl is the length of document d O tfr,d is the term frequency -number of occurrences of t in document d To avoid problem with zero probabilities, we smooth the estimates. First, we define where O Mc is the collection model O cfr is the number of occurrences of t in the collection O T = Σ1cfr is the total number of tokens in the collection We use Pt Mc) to smooth PtId) using Jelinek-Mercer smoothing as Let di The woman who opened fire at YouTube headquarters in Northern California may have been a disgruntled user of the video-sharing site, dz-Authorities are investigating a website that appears to show the same woman accusing YouTube of restricting her videos, and q YouTube fire. Rank di and d with respect to q using Jelinek-Mercer smoothing. Use λ-0.5 Clearly indicate any text normalization procedures performed on documents d1 and d2. Show transcribed image text 1. Consider ranking of documents using the Binary Independence Model (BIM) as shown below: RSVa-2 log where O p is the probability of a term t appearing in a document relevant to the query O (1-p is the probability of a term t not appearing in a document relevant to the query O (1-u) is the probability of a term t not appearing in a document non-relevant to the Shown in Table 1 below are documents, and occurrence of terms (melodic, musical, compo- O ut is the probability of a term t appearing in a document non-relevant to the query query sitions) in the documents. Also shown (in the last row) are relevance judgments (N-non relevant, R relevant) for a query q. Rank the documents for the query q melodic 1 1 0 000 1 1 musical 001 1 0 0 10 1 compositions 0 0 riq,d) RN NRRRR NNR Table 1: Data for ranking by BIM
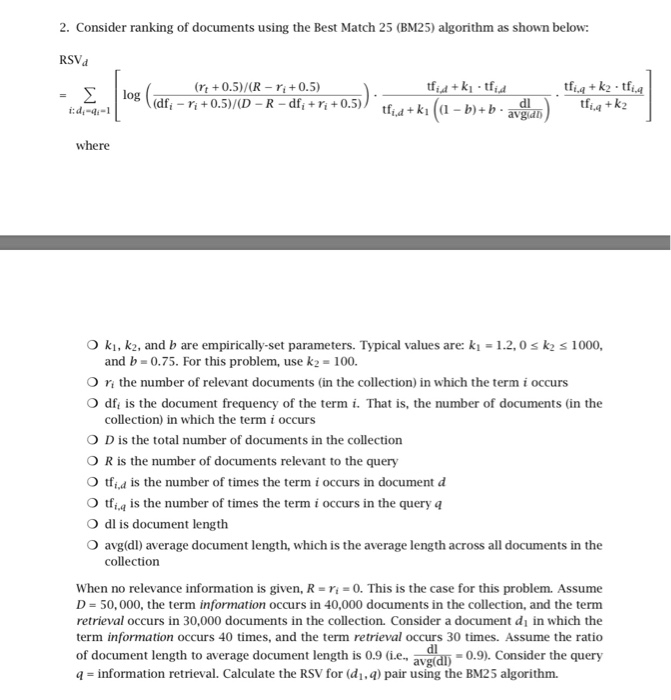
2. Consider ranking of documents using the Best Match 25 (BM25) algorithm as shown below: RSVd tfi.4 + k2 ti.q tfi.ą +k2 (rt +0.5)/(R – ri0.5) (dfi -ri 0.5)/(D -R dfi r0.5) log tfidki -b)+b idi-a-1 avgidl where O ki, k2, and b are empirically-set parameters. Typical values are: ki 리2,0 k2 s1000, and b-0.75. For this problem, use k2-100. o the number of relevant documents (in the collection) in which the term i occurs O dfi is the document frequency of the teri. That is, the number of documents (in the collection) in which the term i occurs O D is the total number of documents in the collection O R is the number of documents relevant to the query O tfia is the number of times the term i occurs in document d O tfi.4 is the number of times the term i occurs in the query q O dl is document length O avg(dl) average document length, which is the average length across all documents in the collection When no relevance information is given, R- 0. This is the case for this problem. Assume D- 50,000, the term information occurs in 40,000 documents in the collection, and the term retrieval occurs in 30,000 documents in the collection. Consider a document di in which the term information occurs 40 times, and the term retrieval occurs 30 times. Assume the ratio gidli 0.9). Consider the query of document length to average document length is 0.9 (i.e., avg(dl) 4-information retrieval. Calculate the RSV for (di)pair using the BM25 algorithm.
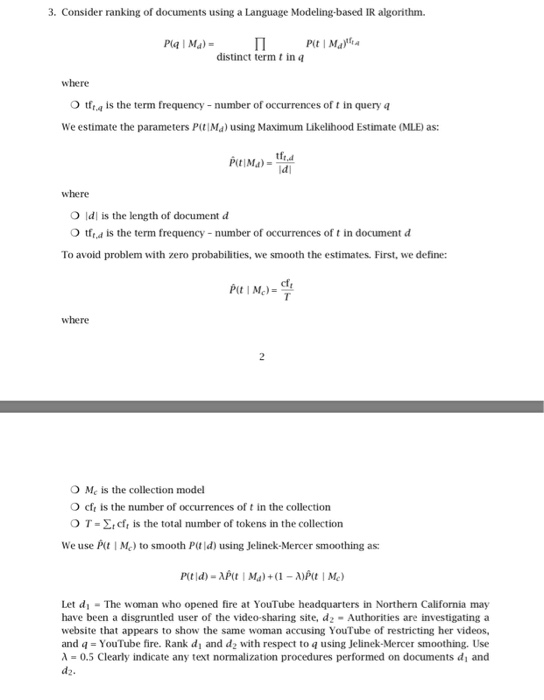
3. Consider ranking of documents using a Language Modeling-based IR algorithm. distinct term t in q where O tr.4 is the term frequency -number of occurrences of t in query a We estimate the parameters PitMa) using Maximum Likelihood Estimate (MLE) as: f,d where O Idl is the length of document d O tfr,d is the term frequency -number of occurrences of t in document d To avoid problem with zero probabilities, we smooth the estimates. First, we define where O Mc is the collection model O cfr is the number of occurrences of t in the collection O T = Σ1cfr is the total number of tokens in the collection We use Pt Mc) to smooth PtId) using Jelinek-Mercer smoothing as Let di The woman who opened fire at YouTube headquarters in Northern California may have been a disgruntled user of the video-sharing site, dz-Authorities are investigating a website that appears to show the same woman accusing YouTube of restricting her videos, and q YouTube fire. Rank di and d with respect to q using Jelinek-Mercer smoothing. Use λ-0.5 Clearly indicate any text normalization procedures performed on documents d1 and d2.
Expert Answer
Answer to 1. Consider ranking of documents using the Binary Independence Model (BIM) as shown below: RSVa-2 log where O p is the p… . . .
[Solved]1 Consider Nonlinear System Cos 2sin Y 1 Use Newton S Method Find Solution System Output E Q37261892
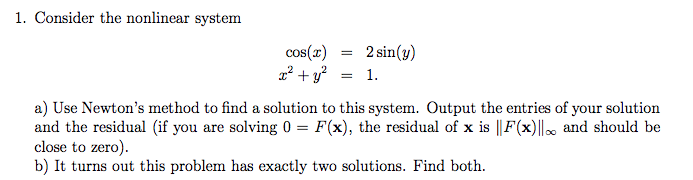
All in Matlab
1. Consider the nonlinear system cos(2sin(y) 1. a) Use Newton’s method to find a solution to this system. Output the entries of your solution and the residual (if you are solving 0 – Fx), the residual of x is F(x) and should be close to zero b) It turns out this problem has exactly two solutions. Find both Show transcribed image text 1. Consider the nonlinear system cos(2sin(y) 1. a) Use Newton’s method to find a solution to this system. Output the entries of your solution and the residual (if you are solving 0 – Fx), the residual of x is F(x) and should be close to zero b) It turns out this problem has exactly two solutions. Find both
Expert Answer
Answer to 1. Consider the nonlinear system cos(2sin(y) 1. a) Use Newton’s method to find a solution to this system. Output the ent… . . .
[Solved]1 Consider T P T Amhamanhuman P Aman Using Na Ve Method Show Steps Many Possible Shifts Ne Q37169765
(1) Consider T and P
T = AMHAMANHUMAN
P = AMAN
Using the Naïve Method show steps on how Many possible shiftsneed to be checked?
Expert Answer
Answer to (1) Consider T and P T = AMHAMANHUMAN P = AMAN Using the Naïve Method show steps on how Many possible shifts need to be… . . .
[Solved]1 Contrast General Design Interest Ui Design 2 Briefly Describe Platform Service Context C Q37181087
1. In contrast to general design, what is of the most interest in UI design? 2. Briefly describe platform as a service in the context of the cloud. . Consider the diagram shown in Figure 10.8 of the Textbook a. How many logical paths are there? List them all. b. How many paths are required to cover all the statements? c. How many paths are required to cover all the branches? 4. Briefly explain the concept of static analysis, and to which software products it can be applied. 5. Describe the steps involved when a customer problem is passed from the customer service/support representative to the technical problem/fix analyst until the problem is resolved Show transcribed image text 1. In contrast to general design, what is of the most interest in UI design? 2. Briefly describe platform as a service in the context of the cloud. . Consider the diagram shown in Figure 10.8 of the Textbook a. How many logical paths are there? List them all. b. How many paths are required to cover all the statements? c. How many paths are required to cover all the branches? 4. Briefly explain the concept of static analysis, and to which software products it can be applied. 5. Describe the steps involved when a customer problem is passed from the customer service/support representative to the technical problem/fix analyst until the problem is resolved
Expert Answer
Answer to 1. In contrast to general design, what is of the most interest in UI design? 2. Briefly describe platform as a service i… . . .

