[Solved]1 Basic Action Processor Must Perform Exception Occurs 2 Implement Exception System Used M Q37191372
1. What is the basic actionthe processor must perform when anexception occurs?
2. To implement the exceptionsystem used in the MIPS architecture,what are the two additionalregisters that we need to add to ourMIPS implementation?Describe the tworegisters.
Expert Answer
Answer to 1. What is the basic action the processor must perform when an exception occurs? 2. To implement the exception system us… . . .
[Solved]1 Bfs Run Breadth First Search Directed Graph Using Vertex 3 Source Show Priority Queue It Q37182405
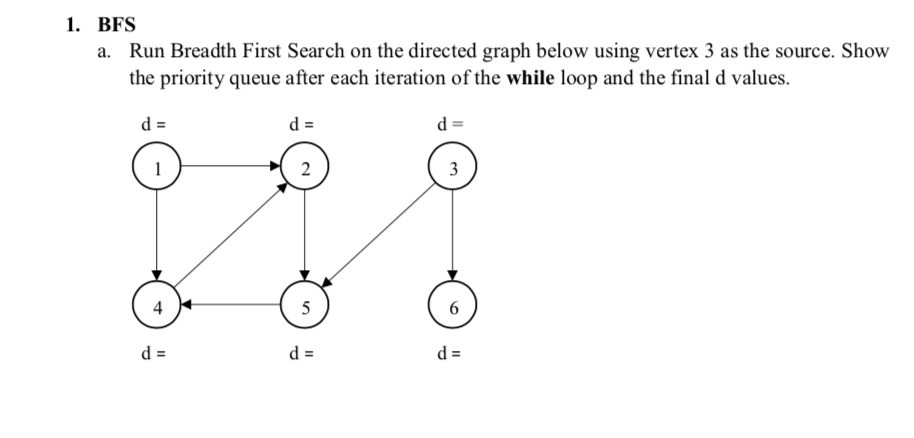
1. BFS Run Breadth First Search on the directed graph below using vertex 3 as the source. Show the priority queue after each iteration of the while loop and the final d values. a. d: 4 Show transcribed image text 1. BFS Run Breadth First Search on the directed graph below using vertex 3 as the source. Show the priority queue after each iteration of the while loop and the final d values. a. d: 4
Expert Answer
Answer to 1. BFS Run Breadth First Search on the directed graph below using vertex 3 as the source. Show the priority queue after … . . .
[Solved]1 Binary Search Tree Create Binary Search Tree Based Given Sequence 5 3 1 10 12 7 9 B Del Q37261127
Explain each step please so i understand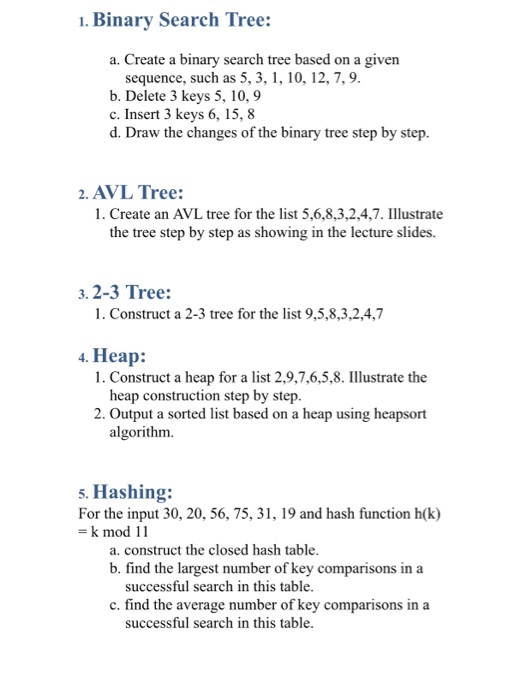 1. Binary Search Tree: a. Create a binary search tree based on a given sequence, such as 5, 3, 1, 10, 12, 7,9 b. Delete 3 keys 5, 10, 9 c. Insert 3 keys 6, 15, 8 d. Draw the changes of the binary tree step by step 2. AVL Tree: 1. Create an AVL tree for the list 5,6,8,3,2.4.7. Illustrate the tree step by step as showing in the lecture slides. 3.2-3 Tree: 1. Construct a 2-3 tree for the list 9,5,8,3,2,4,7 4. Heap: 1. Construct a heap for a list 2,9,7,6,5,8. Illustrate the heap construction step by step 2. Output a sorted list based on a heap using heapsort algorithm. 5. Hashing: For the input 30, 20, 56, 75, 31, 19 and hash function h(k) k mod 11 a. construct the closed hash table successful search in this table. successful search in this table. b. find the largest number of key comparisons in a number of key comparisons in c. find the average a Show transcribed image text 1. Binary Search Tree: a. Create a binary search tree based on a given sequence, such as 5, 3, 1, 10, 12, 7,9 b. Delete 3 keys 5, 10, 9 c. Insert 3 keys 6, 15, 8 d. Draw the changes of the binary tree step by step 2. AVL Tree: 1. Create an AVL tree for the list 5,6,8,3,2.4.7. Illustrate the tree step by step as showing in the lecture slides. 3.2-3 Tree: 1. Construct a 2-3 tree for the list 9,5,8,3,2,4,7 4. Heap: 1. Construct a heap for a list 2,9,7,6,5,8. Illustrate the heap construction step by step 2. Output a sorted list based on a heap using heapsort algorithm. 5. Hashing: For the input 30, 20, 56, 75, 31, 19 and hash function h(k) k mod 11 a. construct the closed hash table successful search in this table. successful search in this table. b. find the largest number of key comparisons in a number of key comparisons in c. find the average a
1. Binary Search Tree: a. Create a binary search tree based on a given sequence, such as 5, 3, 1, 10, 12, 7,9 b. Delete 3 keys 5, 10, 9 c. Insert 3 keys 6, 15, 8 d. Draw the changes of the binary tree step by step 2. AVL Tree: 1. Create an AVL tree for the list 5,6,8,3,2.4.7. Illustrate the tree step by step as showing in the lecture slides. 3.2-3 Tree: 1. Construct a 2-3 tree for the list 9,5,8,3,2,4,7 4. Heap: 1. Construct a heap for a list 2,9,7,6,5,8. Illustrate the heap construction step by step 2. Output a sorted list based on a heap using heapsort algorithm. 5. Hashing: For the input 30, 20, 56, 75, 31, 19 and hash function h(k) k mod 11 a. construct the closed hash table successful search in this table. successful search in this table. b. find the largest number of key comparisons in a number of key comparisons in c. find the average a Show transcribed image text 1. Binary Search Tree: a. Create a binary search tree based on a given sequence, such as 5, 3, 1, 10, 12, 7,9 b. Delete 3 keys 5, 10, 9 c. Insert 3 keys 6, 15, 8 d. Draw the changes of the binary tree step by step 2. AVL Tree: 1. Create an AVL tree for the list 5,6,8,3,2.4.7. Illustrate the tree step by step as showing in the lecture slides. 3.2-3 Tree: 1. Construct a 2-3 tree for the list 9,5,8,3,2,4,7 4. Heap: 1. Construct a heap for a list 2,9,7,6,5,8. Illustrate the heap construction step by step 2. Output a sorted list based on a heap using heapsort algorithm. 5. Hashing: For the input 30, 20, 56, 75, 31, 19 and hash function h(k) k mod 11 a. construct the closed hash table successful search in this table. successful search in this table. b. find the largest number of key comparisons in a number of key comparisons in c. find the average a
Expert Answer
Answer to 1. Binary Search Tree: a. Create a binary search tree based on a given sequence, such as 5, 3, 1, 10, 12, 7,9 b. Delete … . . .
[Solved]1 Caesar Cipher Located Coded Text Plain Character Given Distance Left Right Sequence Cha Q37174279
1. A Caesar cipher located the coded text of plaincharacter.
a. a given distance to the left or right in the sequence ofcharacter
b. an inversion matrix
2. The binary number 111 represents the decimal integer.
a. 111 b.3 c.7
3. Which of the following binary numbers represent the decimalinteger value 8?
a. 11111111
b.100
c. 1000
4. Which file method is used to read the entire content of a filein a single operation?
a. readline
b.read
c. a for loop
Expert Answer
Answer to 1. A Caesar cipher located the coded text of plain character. a. a given distance to the left or right in the sequence o… . . .
[Solved]1 C Assume Gradedata Fstream Object Write Statement Opens File Gradesdat Output Note File Q37251535
1. C++.
Assume that
gradeData
is an
fstream
object, write a statement that opens the file
grades.dat
for output. (
Note: the file is located in the following folderc:Usersjohn
Documents
).
2.
Assume that
diskInfo is an fstream object, write a statement that opens thefile
students.txt for output, where all output will be written to theend of the file.
3.
Write a program that asks the user for the name of a file. Theprogram should display
the first 10 lines of the file on the screen (the “head” of thefile). If the file has
fewer
than 10 lines, the entire file should be displayed, with amessage indicating the entire file has been displayed.
Someone please answer these questions in C++ .
Expert Answer
Answer to 1. C++. Assume that gradeData is an fstream object, write a statement that opens the file grades.dat for output. ( Note:… . . .
[Solved]1 Cell I18 Use Correl Function Determine Relationship Number Wins Team Earned 2010 Amount Q37229920
1. In cell i18, use the CORREL function to determine if there isa relationship between the number of wins a team earned in 2010 andthe amount teams’ salary amount.
2. In cell I21, use the CORREL function to determine if there isa relationship between the number of wins a team earned in 1990 andthe amount teams’ salary amount.
3. In cell I27, use the FORECAST.LINEAR function (or theFORECAST function if you are not using Excel 2016) to determine howmany games a team could expect to win in 2010 if they paid$150,000,000 in salary. Reference the appropriate ranges in thetable and the salary amount as the arguments for your function.
4. In cell I31, use the CONFIDENCE.NORM function to determinethe 95% confidence interval for wins in 2010. Reference theappropriate calculations for size and standard deviation asarguments for your function.
5. In cell I33, calculate the upper limit for the 95% confidenceinterval for your win prediction for a team paying $150,000,000 insalaries. Reference your prediction and the confidence intervalcalculation for your formula.
6. In cell I35, calculate the lower limit for the 95% confidenceinterval for your win prediction for a team paying $150,000,000 insalaries. Reference your prediction and the confidence intervalcalculation for your formula.
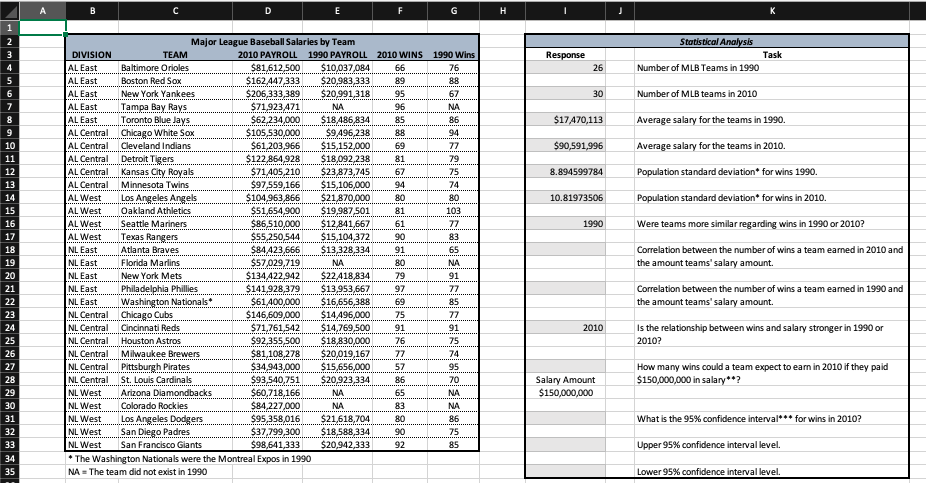
Major League Baseball Salaries by Team 2010 PAYROLL 1990 PAYROLL 2010 WINS 1990 Wins 76 DIVISION Baltimore Orioles 81,612 500S10037084 66 162AA333O83, 33382 206333389 S201318.9S 26 Number of MLB Teams in 1990 Eas Boston Red Sox AL East New York Yankees 30 Number of MLB teams in 2010 AL EastT LE Toronto Blue Jays L Cetral.IChicago White So AL Central Cleveland Indians AL Central Detroit Tigers ALCentra..Kansas City Royals AL Central Minnesota Twins Tampa Bay Rays 7123 471 62,234,00o$18486 83485 105 53000oS9496 238..88 61,203 966S1515200069 12286498S18,092 238..81 $71 405.210$23 873 745 67 9166S15,106,00094 $104 963 866$21 870 00080 5165,00$19.987,50181 86.510000128416661 5S250 544$15,1043290 $17A70,113Average slary for the teams in 1990 S90591996 Averagesalary for the teams in 2010. Population standard deviation for wins 1990. Population standard deviation for wins in 2010. Were teams more similar regarding wins in 1990 or 2010? Correlation between the number of wins a team eaned in 2010 and -8.894599784 13 LWest . Los Angeles Anges AL West Oakland Athletics AL West Seattle Mariners ALWes.TexasRangers 10.81973506 16 4 423 666$13328 334 $57,029,719 Atlanta Braves Florida Marlins New York Mets NL East the amount teams’ salary amount NL as.Philadelphia Phillies NL Eas.Washington Nationas NL Central Chicago Cubs NL Centra Cincinnati Reds NL Central Houston Astros 141.928379S13953,6697 $61400,000 $16,656,3886 Correlation between the number of wins a team eaned in 1990 and the amount teams’ salary amount 23 146.6000S14496,000..75 $71,761,542 $14,769,5009 $92,355,500 $18830,00076 2010 Is the relationship between wins and salary stronger in 1990 or 2010? 25 26 Miwaukee Brewer.S811082S20019,16777 NL Central. Pittsburgh Pirates NL Centra St. Louis Cardinals NL West Arizona Diamondbacks NL West Colorado Rockies $34943,000 $15,656,000 57 How many wins could a team expect to earn in 2010 if they paid $150,000,000 in salary2 540..S209233386 Salary Amount 84 227000 NL West . Los Angeles Do NL West..San Diego Padres $95,358,016 $21,618,704 80 7799300 $18588334 go $98,641,333 $20,942,333 92 what is the 95% confidence interval for wins in 2010? 32 75 NL West Sn Francisco Giants The Washington Nationals were the Montreal Expos in 1990 NA The team did not exist in 1990 Upper 95% confidence interval level. 34 Lower 95% confidence interval level Show transcribed image text Major League Baseball Salaries by Team 2010 PAYROLL 1990 PAYROLL 2010 WINS 1990 Wins 76 DIVISION Baltimore Orioles 81,612 500S10037084 66 162AA333O83, 33382 206333389 S201318.9S 26 Number of MLB Teams in 1990 Eas Boston Red Sox AL East New York Yankees 30 Number of MLB teams in 2010 AL EastT LE Toronto Blue Jays L Cetral.IChicago White So AL Central Cleveland Indians AL Central Detroit Tigers ALCentra..Kansas City Royals AL Central Minnesota Twins Tampa Bay Rays 7123 471 62,234,00o$18486 83485 105 53000oS9496 238..88 61,203 966S1515200069 12286498S18,092 238..81 $71 405.210$23 873 745 67 9166S15,106,00094 $104 963 866$21 870 00080 5165,00$19.987,50181 86.510000128416661 5S250 544$15,1043290 $17A70,113Average slary for the teams in 1990 S90591996 Averagesalary for the teams in 2010. Population standard deviation for wins 1990. Population standard deviation for wins in 2010. Were teams more similar regarding wins in 1990 or 2010? Correlation between the number of wins a team eaned in 2010 and -8.894599784 13 LWest . Los Angeles Anges AL West Oakland Athletics AL West Seattle Mariners ALWes.TexasRangers 10.81973506 16 4 423 666$13328 334 $57,029,719 Atlanta Braves Florida Marlins New York Mets NL East the amount teams’ salary amount NL as.Philadelphia Phillies NL Eas.Washington Nationas NL Central Chicago Cubs NL Centra Cincinnati Reds NL Central Houston Astros 141.928379S13953,6697 $61400,000 $16,656,3886 Correlation between the number of wins a team eaned in 1990 and the amount teams’ salary amount 23 146.6000S14496,000..75 $71,761,542 $14,769,5009 $92,355,500 $18830,00076 2010 Is the relationship between wins and salary stronger in 1990 or 2010? 25 26 Miwaukee Brewer.S811082S20019,16777 NL Central. Pittsburgh Pirates NL Centra St. Louis Cardinals NL West Arizona Diamondbacks NL West Colorado Rockies $34943,000 $15,656,000 57 How many wins could a team expect to earn in 2010 if they paid $150,000,000 in salary2 540..S209233386 Salary Amount 84 227000 NL West . Los Angeles Do NL West..San Diego Padres $95,358,016 $21,618,704 80 7799300 $18588334 go $98,641,333 $20,942,333 92 what is the 95% confidence interval for wins in 2010? 32 75 NL West Sn Francisco Giants The Washington Nationals were the Montreal Expos in 1990 NA The team did not exist in 1990 Upper 95% confidence interval level. 34 Lower 95% confidence interval level
Expert Answer
Answer to 1. In cell i18, use the CORREL function to determine if there is a relationship between the number of wins a team earned… . . .
[Solved]1 Complete Following Method Takes String Parameter Time American 12 Hour Format 06 12 Pm M Q37291384
1. Complete the following method that takes a String parameterthat is a time in American 12 hour format, such as “06:12PM.”
The method returns a String with the same time in standardinternational 24 hour form. For example, given the parameter in theexample above, the method would return “18:12.” Values with AMcorrespond to times from 00:00 to 11:59 and PM for times from 12:00to 23:59.
Recall the method Integer.parseInt() takes a String parameter andreturns the integer equivalent.
// precondition: the String value of the time parameter is validand
// has a length of 8 characters.
public static String convertTime(String amerFormat)
{
}
2.
Complete the DiskDrive class shown below. A DiskDrive keepstrack of how much disk space is used and how much is free. Themaximum size of the drive is a parameter to the constructor. Theoccupied space on the drive can never exceed the maximum size ofthe drive and can never go below zero.
public class DiskDrive
{
// declare instance variables
// postcondition: all instancevariables are initialized
public DiskDrive(doublesizeCapacity)
{
}
// postcondition: the disk spaceoccupied is increased by the amount given by the
// parameter and cannot exceed themaximum
public void addFile(doublesize)
{
}
// postcondition: the disk spaceoccupied is decreased by the amount given by the
// parameter and cannot benegative
public void deleteFile(doublesize)
{
}
// postcondition: a quantity equal tothe unoccupied disk space is provided and is
// not negative
public double getFreeSpace()
{
}
// other methods not shown
}
Expert Answer
Answer to 1. Complete the following method that takes a String parameter that is a time in American 12 hour format, such as “06:12… . . .
[Solved]1 Chapter 1 Created Class Called Randomguess Game Application Generates Random Number Play Q37295245
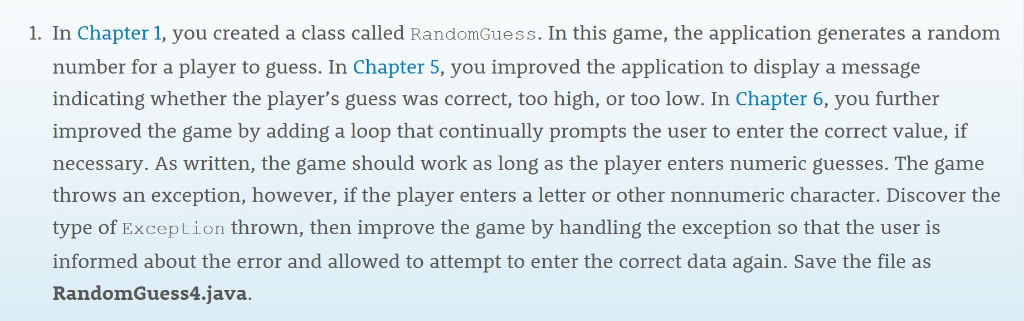
1. In Chapter 1, you created a class called RandomGuess. In this game, the application generates a random number for a player to guess. In Chapter 5, you improved the application to display a message indicating whether the player’s guess was correct, too high, or too low. In Chapter 6, you further improved the game by adding a loop that continually prompts the user to enter the correct value, if necessary. As written, the game should work as long as the player enters numeric guesses. The game throws an exception, however, if the player enters a letter or other nonnumeric character. Discover the type of Exception thrown, then improve the game by handling the exception so that the user is informed about the error and allowed to attempt to enter the correct data again. Save the file as RandomGuess4.java. Show transcribed image text 1. In Chapter 1, you created a class called RandomGuess. In this game, the application generates a random number for a player to guess. In Chapter 5, you improved the application to display a message indicating whether the player’s guess was correct, too high, or too low. In Chapter 6, you further improved the game by adding a loop that continually prompts the user to enter the correct value, if necessary. As written, the game should work as long as the player enters numeric guesses. The game throws an exception, however, if the player enters a letter or other nonnumeric character. Discover the type of Exception thrown, then improve the game by handling the exception so that the user is informed about the error and allowed to attempt to enter the correct data again. Save the file as RandomGuess4.java.
Expert Answer
Answer to 1. In Chapter 1, you created a class called RandomGuess. In this game, the application generates a random number for a p… . . .
[Solved]1 Complete Payoffs Following Game Potential Game L C R 1 M 45 32 Q37244988
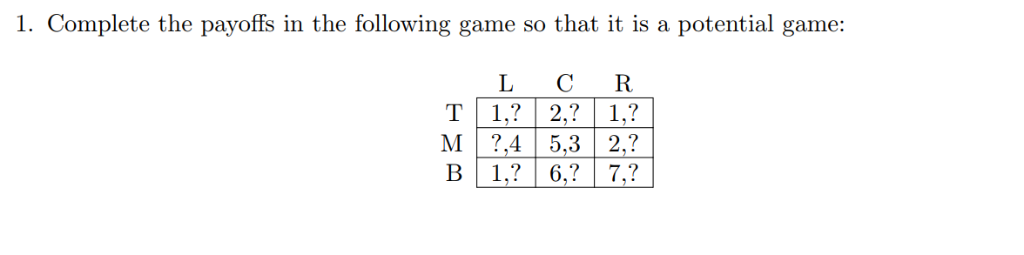
1. Complete the payoffs in the following game so that it is a potential game: L C R 1 M ,45,32,? Show transcribed image text 1. Complete the payoffs in the following game so that it is a potential game: L C R 1 M ,45,32,?
Expert Answer
Answer to 1. Complete the payoffs in the following game so that it is a potential game: L C R 1 M ,45,32,?… . . .
[Solved]1 Computer Fraud Abuse Act Cfaa First Enacted 1986 Still Enforced Today Generally Law Used Q37186437
1) Computer Fraud and Abuse Act (or CFAA), which was firstenacted in 1986, is still enforced today. Generally, this law isused to deter and to punish individuals for their unauthorizedaccess of computers. As we’ve learned, the CFAA has been appliedbroadly to a number of situations and has been subject to a lot ofcontroversy. Consider the following story about Aaron Swartz: ayoung digital activist who faced a maximum of $1 million in finesand 35 years in prison under the CFAA and other federal statutes.Today, we’re going to learn about Swartz’ story and find out why hefaced such a hefty penalty. Although Swartz passed away in 2013,his story lives on and is a hotly debated topic in cyberlaw.
First, watch the Aaron Swartz video:https://www.youtube.com/watch?v=0MUjdc3KIYA
(Write 200 words) answer the followingquestions:
1.1) In your own words, define the word “hacktivism.”
1.2) Do you feel that Aaron Swartz fit the definition as a“hacktivist?” Why or why not?
1.3) After watching the video, what surprised you about AaronSwartz’ case? Do you feel that this type of penalty was just?
1.4) Pretend you are creating a new computer law that punishesunauthorized access to computers.
a) What types of penalties would you impose on people whoviolate the law?
b) Would they be the same for every type of attack?
Expert Answer
Answer to 1) Computer Fraud and Abuse Act (or CFAA), which was first enacted in 1986, is still enforced today. Generally, this law… . . .

