[Solved]1 15 Pts Implement Recursive Memoized Dynamic Programming Fibonacci Study Performances Usi Q37232414
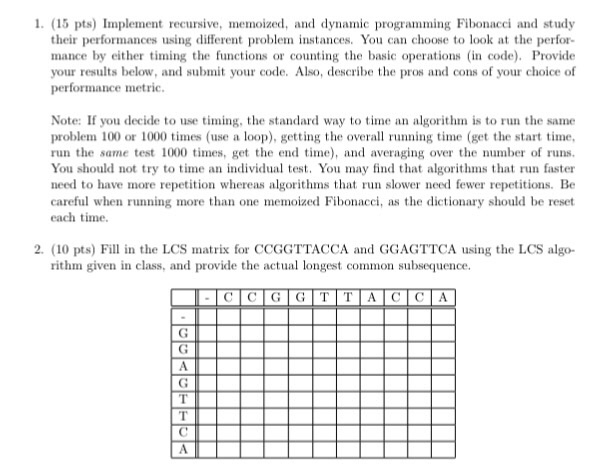 1 (15 pts) Implement recursive, memoized, and dynamic programming Fibonacci and study their performances using different problem instans You can choose to look at the perfor- mance by either timing the functions or counting the basic operations (in code) Provide your results below, and submit your code. Also, describe the pros and cons of your choice of performance metric Note: If you decide to use timing, the standard way to time an algorithm is to run the same problem 100 or 1000 times (use a loop), getting the overall running time (get the start time run the same test 1000 times, get the end ti and averaging over the number of runs. You should not try to time an individual test. You may find that algorithms that run faster need to have more repetition whereas algorithms that ru slower need fewer repetitions. Be careful when running mo hanone memoized Fibonacci, as the dictionary should be reset each time, 2. (10 pts) Fill in the LCS matrix for CCGGTTACCA and GGAGTTCA using the LCS algo- rithm given in class, and provide the actual longest common subsequence Show transcribed image text 1 (15 pts) Implement recursive, memoized, and dynamic programming Fibonacci and study their performances using different problem instans You can choose to look at the perfor- mance by either timing the functions or counting the basic operations (in code) Provide your results below, and submit your code. Also, describe the pros and cons of your choice of performance metric Note: If you decide to use timing, the standard way to time an algorithm is to run the same problem 100 or 1000 times (use a loop), getting the overall running time (get the start time run the same test 1000 times, get the end ti and averaging over the number of runs. You should not try to time an individual test. You may find that algorithms that run faster need to have more repetition whereas algorithms that ru slower need fewer repetitions. Be careful when running mo hanone memoized Fibonacci, as the dictionary should be reset each time, 2. (10 pts) Fill in the LCS matrix for CCGGTTACCA and GGAGTTCA using the LCS algo- rithm given in class, and provide the actual longest common subsequence
1 (15 pts) Implement recursive, memoized, and dynamic programming Fibonacci and study their performances using different problem instans You can choose to look at the perfor- mance by either timing the functions or counting the basic operations (in code) Provide your results below, and submit your code. Also, describe the pros and cons of your choice of performance metric Note: If you decide to use timing, the standard way to time an algorithm is to run the same problem 100 or 1000 times (use a loop), getting the overall running time (get the start time run the same test 1000 times, get the end ti and averaging over the number of runs. You should not try to time an individual test. You may find that algorithms that run faster need to have more repetition whereas algorithms that ru slower need fewer repetitions. Be careful when running mo hanone memoized Fibonacci, as the dictionary should be reset each time, 2. (10 pts) Fill in the LCS matrix for CCGGTTACCA and GGAGTTCA using the LCS algo- rithm given in class, and provide the actual longest common subsequence Show transcribed image text 1 (15 pts) Implement recursive, memoized, and dynamic programming Fibonacci and study their performances using different problem instans You can choose to look at the perfor- mance by either timing the functions or counting the basic operations (in code) Provide your results below, and submit your code. Also, describe the pros and cons of your choice of performance metric Note: If you decide to use timing, the standard way to time an algorithm is to run the same problem 100 or 1000 times (use a loop), getting the overall running time (get the start time run the same test 1000 times, get the end ti and averaging over the number of runs. You should not try to time an individual test. You may find that algorithms that run faster need to have more repetition whereas algorithms that ru slower need fewer repetitions. Be careful when running mo hanone memoized Fibonacci, as the dictionary should be reset each time, 2. (10 pts) Fill in the LCS matrix for CCGGTTACCA and GGAGTTCA using the LCS algo- rithm given in class, and provide the actual longest common subsequence
Expert Answer
Answer to 1 (15 pts) Implement recursive, memoized, and dynamic programming Fibonacci and study their performances using different… . . .
[Solved]1 2 Marks Convert 7777 Decimal Binary Hexadecimal Show Steps Q37247230
Could you solve it in clear steps please #1, (2 marks) convert 7777 from decimal to binary, and then to hexadecimal. Show your steps. Show transcribed image text #1, (2 marks) convert 7777 from decimal to binary, and then to hexadecimal. Show your steps.
#1, (2 marks) convert 7777 from decimal to binary, and then to hexadecimal. Show your steps. Show transcribed image text #1, (2 marks) convert 7777 from decimal to binary, and then to hexadecimal. Show your steps.
Expert Answer
Answer to #1, (2 marks) convert 7777 from decimal to binary, and then to hexadecimal. Show your steps…. . . .
[Solved]1 2 Question 2 30 Points Network Shown Figure 2 Snapshot Practical Network Consisting Seve Q37184642
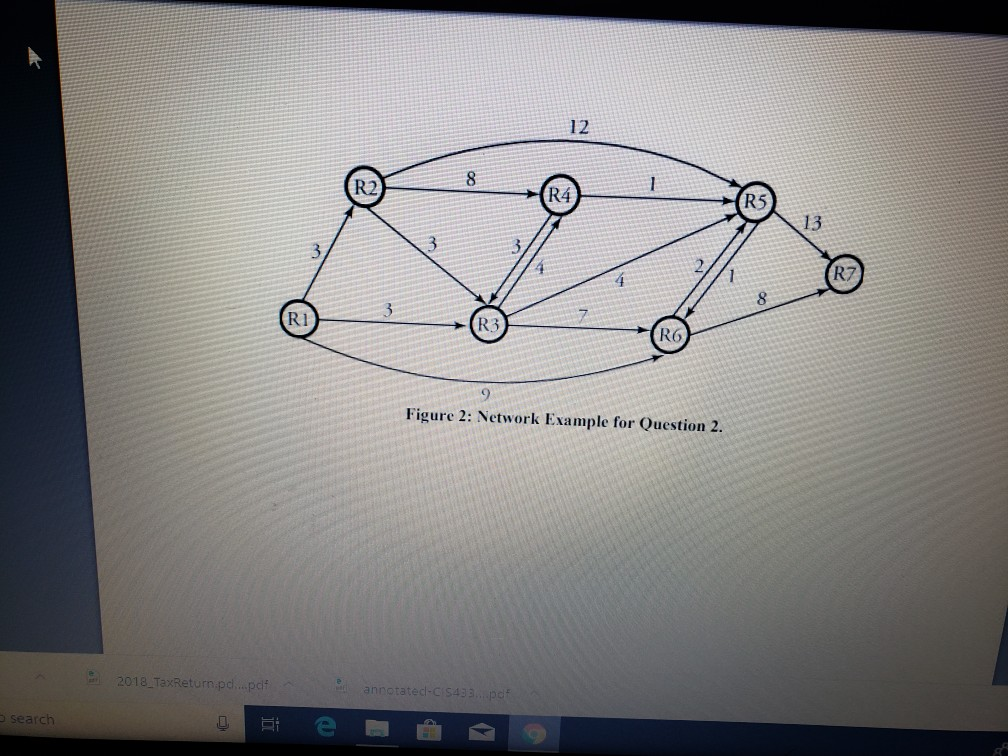
12 R2 R4 R5 13 2 R7 4 ICE) R3 R1 R6 Figure 2: Network Example for Question 2. 2018 TaxReturn pd…pd search
Expert Answer
Answer to 1/2 Question 2: 30 points The network shown in Figure 2 is a snapshot of a practical network consisting of seven routers… . . .
[Solved]1 20 Points 10 Bit Message M 1010011110 Encoded Crc Code Using Genertor Polynomial P X 1 X Q37230803
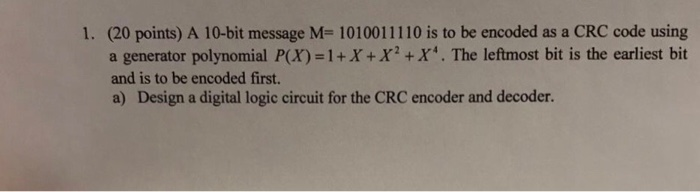
 1. (20 points) A 10-bit message M- 1010011110 is to be encoded as a CRC code using a genertor polynomial P(X)=1 + X+X2 +X4. The leftmost bit is the earliest bit and is to be encoded first. a) Design a digital logic circuit for the CRC encoder and decoder. b) If the received sequence is Tr-1010001101, is there any ertor in the transmission Using the digital logic circuit obtained in a), illustrate the decoding procedure showing each step of decoding and the states of the registers in each step. Show transcribed image text 1. (20 points) A 10-bit message M- 1010011110 is to be encoded as a CRC code using a genertor polynomial P(X)=1 + X+X2 +X4. The leftmost bit is the earliest bit and is to be encoded first. a) Design a digital logic circuit for the CRC encoder and decoder.
1. (20 points) A 10-bit message M- 1010011110 is to be encoded as a CRC code using a genertor polynomial P(X)=1 + X+X2 +X4. The leftmost bit is the earliest bit and is to be encoded first. a) Design a digital logic circuit for the CRC encoder and decoder. b) If the received sequence is Tr-1010001101, is there any ertor in the transmission Using the digital logic circuit obtained in a), illustrate the decoding procedure showing each step of decoding and the states of the registers in each step. Show transcribed image text 1. (20 points) A 10-bit message M- 1010011110 is to be encoded as a CRC code using a genertor polynomial P(X)=1 + X+X2 +X4. The leftmost bit is the earliest bit and is to be encoded first. a) Design a digital logic circuit for the CRC encoder and decoder.
b) If the received sequence is Tr-1010001101, is there any ertor in the transmission Using the digital logic circuit obtained in a), illustrate the decoding procedure showing each step of decoding and the states of the registers in each step.
Expert Answer
Answer to 1. (20 points) A 10-bit message M- 1010011110 is to be encoded as a CRC code using a genertor polynomial P(X)=1 + X+X2 +… . . .
[Solved]1 20 Illustrate Operations Heapsort Array Drawing Heap Step 7 8 1 12 5 4 3 1 Build Initial Q37254967
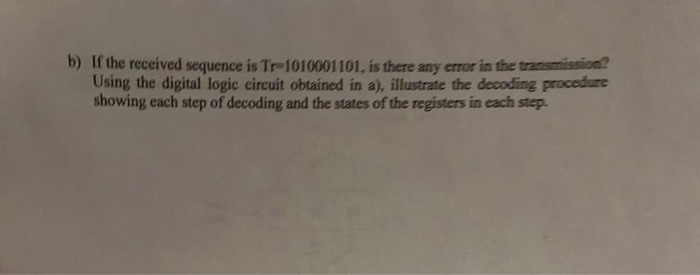
 1. (20%) Illustrate the operations of Heapsort on the array A drawing the heap in each step. 7,8, 1, 12, 5, 4, 3) by 1) Build the initial heap in either top-down or bottom-up 2) Sort the elements. Show transcribed image text 1. (20%) Illustrate the operations of Heapsort on the array A drawing the heap in each step. 7,8, 1, 12, 5, 4, 3) by 1) Build the initial heap in either top-down or bottom-up 2) Sort the elements.
1. (20%) Illustrate the operations of Heapsort on the array A drawing the heap in each step. 7,8, 1, 12, 5, 4, 3) by 1) Build the initial heap in either top-down or bottom-up 2) Sort the elements. Show transcribed image text 1. (20%) Illustrate the operations of Heapsort on the array A drawing the heap in each step. 7,8, 1, 12, 5, 4, 3) by 1) Build the initial heap in either top-down or bottom-up 2) Sort the elements.
Expert Answer
Answer to 1. (20%) Illustrate the operations of Heapsort on the array A drawing the heap in each step. 7,8, 1, 12, 5, 4, 3) by 1) … . . .
[Solved]1 20 Points Minimum Spanning Trees Roads Suppose Given Following Connected Undirected Weig Q37195066
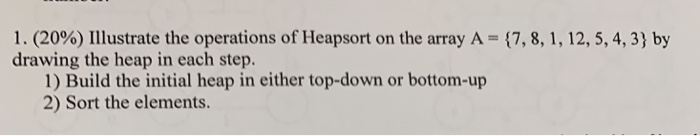
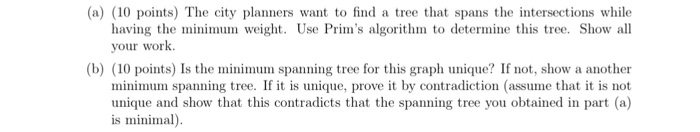 1. (20 points) Minimum Spanning Trees in Roads. Suppose you are given the following connected, undirected, weighted graph where the vertices represent intersections in a city and the edges are the roads connecting these intersections. The weights on the edges represent the relative traffic congestion (the larger the weight, the more congested the road is) U4 02 12 10 07 13 4 14 0 01 (a) (10 points) The city planners want to find a tree that spans the intersections while having the minimum weight. Use Prim’s algorithm to determine this tree. Show all your work (b) (10 points) Is the minimum spanning tree for this graph unique? If not, show a another minimum spanning tree. If it is unique, prove it by contradiction (assume that it is not unique and show that this contradicts that the spanning tree you obtained in part (a) is minimal) Show transcribed image text 1. (20 points) Minimum Spanning Trees in Roads. Suppose you are given the following connected, undirected, weighted graph where the vertices represent intersections in a city and the edges are the roads connecting these intersections. The weights on the edges represent the relative traffic congestion (the larger the weight, the more congested the road is) U4 02 12 10 07 13 4 14 0 01
1. (20 points) Minimum Spanning Trees in Roads. Suppose you are given the following connected, undirected, weighted graph where the vertices represent intersections in a city and the edges are the roads connecting these intersections. The weights on the edges represent the relative traffic congestion (the larger the weight, the more congested the road is) U4 02 12 10 07 13 4 14 0 01 (a) (10 points) The city planners want to find a tree that spans the intersections while having the minimum weight. Use Prim’s algorithm to determine this tree. Show all your work (b) (10 points) Is the minimum spanning tree for this graph unique? If not, show a another minimum spanning tree. If it is unique, prove it by contradiction (assume that it is not unique and show that this contradicts that the spanning tree you obtained in part (a) is minimal) Show transcribed image text 1. (20 points) Minimum Spanning Trees in Roads. Suppose you are given the following connected, undirected, weighted graph where the vertices represent intersections in a city and the edges are the roads connecting these intersections. The weights on the edges represent the relative traffic congestion (the larger the weight, the more congested the road is) U4 02 12 10 07 13 4 14 0 01
(a) (10 points) The city planners want to find a tree that spans the intersections while having the minimum weight. Use Prim’s algorithm to determine this tree. Show all your work (b) (10 points) Is the minimum spanning tree for this graph unique? If not, show a another minimum spanning tree. If it is unique, prove it by contradiction (assume that it is not unique and show that this contradicts that the spanning tree you obtained in part (a) is minimal)
Expert Answer
Answer to 1. (20 points) Minimum Spanning Trees in Roads. Suppose you are given the following connected, undirected, weighted grap… . . .
[Solved]1 20 Points Following Table Provides Parameters Different Caches C Cache Size Bytes B Bloc Q37284711
![1.[20 points] The following table provides parameters for different caches. C is the cache size (bytes), B is the block size](https://media.cheggcdn.com/media%2F5fd%2F5fdef8ea-1b4b-4efc-b9c0-6de6cc9740aa%2FphpNIFd7S.png)
1.[20 points] The following table provides parameters for different caches. C is the cache size (bytes), B is the block size (bytes) and E is the associativity. Assume a 32-bit address space. For each cache, calculate the number of cache sets (S), number of tag bits (t), number of set index bits (s) and number of block offset bits (b) Cache C B E S t s b 1024 4 4 – – – – 1024 4 256 – – – – 1024 8 1 – – – 1024 8 128 – – – Show transcribed image text 1.[20 points] The following table provides parameters for different caches. C is the cache size (bytes), B is the block size (bytes) and E is the associativity. Assume a 32-bit address space. For each cache, calculate the number of cache sets (S), number of tag bits (t), number of set index bits (s) and number of block offset bits (b) Cache C B E S t s b 1024 4 4 – – – – 1024 4 256 – – – – 1024 8 1 – – – 1024 8 128 – – –
Expert Answer
Answer to 1.[20 points] The following table provides parameters for different caches. C is the cache size (bytes), B is the block … . . .
[Solved]1 20 Points Suppose Disposal Worst Case Linear Time Median Subroutine Called Black Box Tak Q37200576
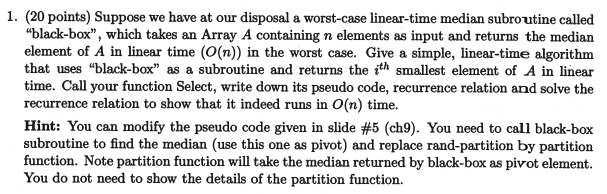
1. (20 points) Suppose we have at our disposal a worst-case linear-time median subroutine called “black-box”, which takes an Array A containing n elements as input and returns the median element of A in linear time (O(n)) in the worst case. Give a simple, linear-time algorithm that uses “black-box” as a subroutine and returns the ith smallest element of A in linear time. Call your function Select, write down its pseudo code, recurrence relation and solve the recurrence relation to show that it indeed runs in O(n) time. Hint: You can modify the pseudo code given in slide #5 (ch9). You need to call black-box subroutine to find the median (use this one as pivot) and replace rand-partition by partition function. Note partition function will take the median returned by black-box as pivot element. You do not need to show the details of the partition function. Randomized divide-and- conquer algorithm RAND-SELECT(A, p, q, i returns i th smallest of A[ p.. ql if p q &i > 1 then error! r ← RAND-PARTITION(A, p, q) kr-p+1 if i=k then return A[r] if i〈k rank(A[r]) k then return RAND-SELECT(A, p, r-1, i) else return RAND-SELECT(A, r + 1, q, i -k) S A[r] Show transcribed image text 1. (20 points) Suppose we have at our disposal a worst-case linear-time median subroutine called “black-box”, which takes an Array A containing n elements as input and returns the median element of A in linear time (O(n)) in the worst case. Give a simple, linear-time algorithm that uses “black-box” as a subroutine and returns the ith smallest element of A in linear time. Call your function Select, write down its pseudo code, recurrence relation and solve the recurrence relation to show that it indeed runs in O(n) time. Hint: You can modify the pseudo code given in slide #5 (ch9). You need to call black-box subroutine to find the median (use this one as pivot) and replace rand-partition by partition function. Note partition function will take the median returned by black-box as pivot element. You do not need to show the details of the partition function.
Randomized divide-and- conquer algorithm RAND-SELECT(A, p, q, i returns i th smallest of A[ p.. ql if p q &i > 1 then error! r ← RAND-PARTITION(A, p, q) kr-p+1 if i=k then return A[r] if i〈k rank(A[r]) k then return RAND-SELECT(A, p, r-1, i) else return RAND-SELECT(A, r + 1, q, i -k) S A[r]
Expert Answer
Answer to 1. (20 points) Suppose we have at our disposal a worst-case linear-time median subroutine called “black-box”, which take… . . .
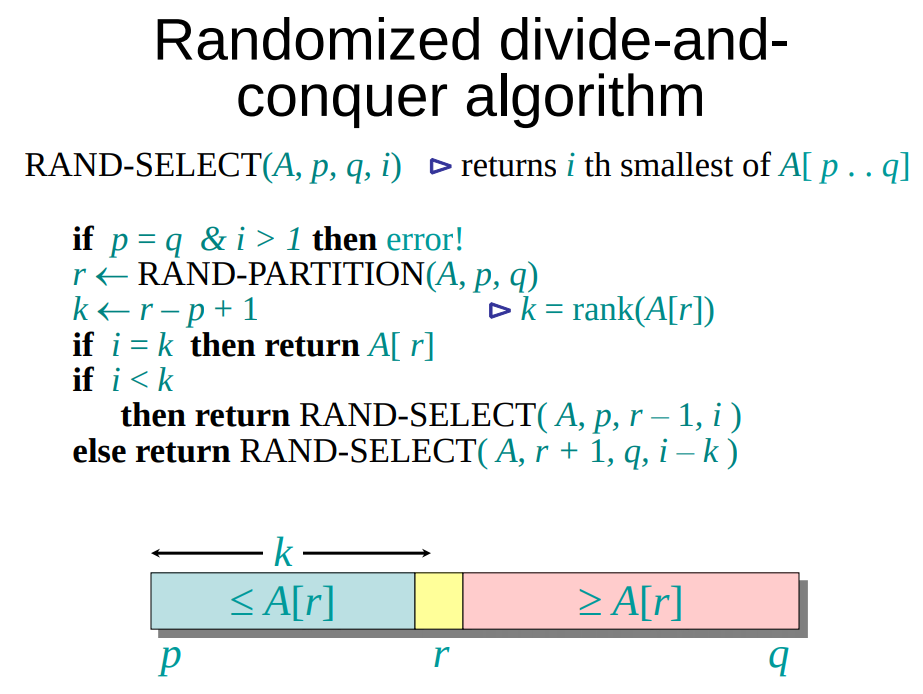
[Solved]1 20p Consider Flow Network Given 3 S Source T Sink 1 10p Simulate Edmonds Karp Algorithm Q37237225
1. (20p) Consider the flow network given below 3 where s is the source and t is the sink. 1. (10p) Simulate the Edmonds-Karp algorithm to find a flow with marimum value, M. Show transcribed image text 1. (20p) Consider the flow network given below 3 where s is the source and t is the sink. 1. (10p) Simulate the Edmonds-Karp algorithm to find a flow with marimum value, M.
Expert Answer
Answer to 1. (20p) Consider the flow network given below 3 where s is the source and t is the sink. 1. (10p) Simulate the Edmonds-… . . .
[Solved]1 20 Pts Complete Class Time Stores Manipulates Times 24 Hour Clock Specified Write Requir Q37249709
1. (20 pts) Complete the class Time, which stores andmanipulates times on a 24-hour clock. As specified below, write therequired methods, including those needed for overloading operators.Exceptions messages should include the class and method names, andidentify the error (including the value of all relevant arguments).Hint see the type_as_str function in the goody.py module.
-
The class is initialized with three int values (the hour first,the minute second, the second third; all with default values of 0).If any parameter is not an int, or not in the correct range (thehour must be between 0 and 23 inclusive, the minute and second mustbe between 0 and 59 inclusive) raise an AssertionError with anappropriate string describing the problem/values. When initialized,the Time class should create exactly three attributes/selfvariables named hour, minute, and second (with these exact namesand no others attributes/self variables).
-
Write the __getitem__ method to allow Time class objects to beindexed by either (a) an int with value 1 or 2 or 3, or (b) anylength tuple containing any combinations of just these threevalues: e.g., (1,3). If the index is not one of these types orvalues, raise an IndexError exception with an appropriate stringdescribing the problem/values. If the argument is 1, returns thehour; if the argument is 2, return the minute, and if the argumentis 3, return the second. If the argument is a tuple, return a tuplewith hour or minute or second substituted for each value in thetuple. So if t = Time(5,15,20) then t[1] returns 5 and t[2,3]returns (15,20). Note that calling t[1] will pass 1 as itsargument; calling t[1,2] will pass the tuple (1,2) as its argument.In fact, t[1,1] will pass the tuple (1,1) and return the tuple(5,5).
-
Write methods that return (a) the standard repr function of aTime, and (b) a str function of a Time: str for a Time shows thetime in the standard 12 hour clock format: str(Time(13,10,5))returns ‘1:10:05pm’; str(Time(5,6,3)) returns ‘5:06:03am’;str(Time(0,0,0)) returns ’12:00:00am’. It is critical to write thestr method correctly, because I used it in the batch self-checkfile for testing the correctness of other methods.
-
Write a method that interprets midnight as False and any othertime as True.
-
Write a method that interprets the length of a Time as thenumber of seconds that have elapsed from midnight to the that time.So len(Time(0,0,0)) returns 0 and len(Time(23,59,59)) returns86,399; there are 86,400 seconds in a day: midnight tomidnight.
-
Overload the == operator to allow comparing two Time objects forequality (if a time object is compared against an object from anyother class, it should return False). Note that if you define ==correctly, Python will be able to compute != by using not and==.
-
Overload the < operator to allow comparing two Time objects.The left Time is less-than the right one if it comes earlier in theday than the right one. Also allow the right operand to be an int:in this case, return whether the length (an int, see above) of theTime is less-than the right int. If the right operand is any othertype, raise a TypeError exception with an appropriate stringdescribing the problem/values. Note that if you define <correctly, Python will be able to compute Time > Time and int> Time by using <.
-
Overload the + operator to allow adding a Time object and anint, producing a new Time object as a result (and not mutating theTime object + was called on). If the other operand is not an int,raise a TypeError
exception with an appropriate string describing theproblem/values (you may assume without checking that this argumentis non-negative). Both Time + int and int + Time should be allowedand have the same meaning. Hint: write code that adds one second toa Time; then iterate over this code the int number of times: thereare faster ways to do this, but this way is correct.
9. Write the __call__ method to allow an object from this classto be callable with three int arguments: update the hour of theobject to be the first argument, and the minute of the object to bethe secondargument,andthesecondoftheobjecttobethethirdargument.ReturnNone.Ifanyparameterisnotlegal (see how the class is initialized), raisean AssertionError with an appropriate string describing theproblem/values.
Expert Answer
Answer to 1. (20 pts) Complete the class Time, which stores and manipulates times on a 24-hour clock. As specified below, write th… . . .

