[Solved]Suppose Private Key File S1 Object O1 S1 Read Suppose Public Key File S1 Object 02 Read S1 Q37206945
Can someone help me with some questions please
1. 
2. 
4. 
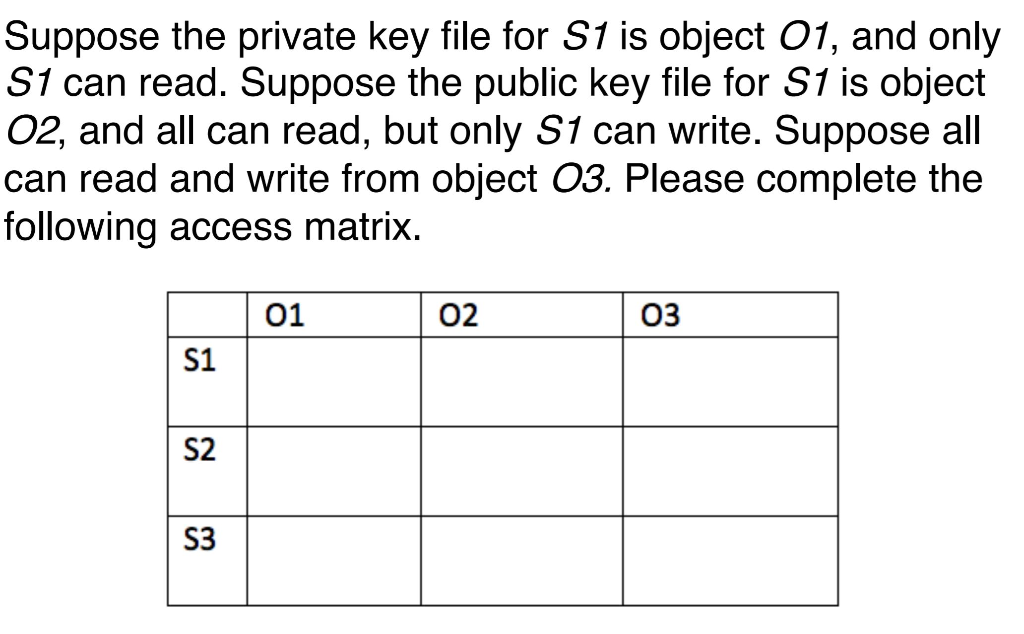
Suppose the private key file for S1 is object O1, and only S1 can read. Suppose the public key file for S1 is object 02, and all can read, but only S1 can write. Suppose all can read and write from object 03. Please complete the following access matrix. 03 02 01 S1 S2 S3 Explain the effect of the firewall rule set as given below Note that port 80 is the port a Web server expects to receive from a Web client, while port 25 is the port a host listens to for Simple Mail Transfer Protocol (SMTP) requests. SourceDestination Addr Destination Action Direction Source Addr Port Port 80 nytimes.com Allow Allow Block Out In Either 129.252.131.2 25 . Assume that a database only stores the sha256 value for the username. The following SQL statement is sent to the database, where the values of the $uName will be replaced by the value that the user provides . (1) Does this program have a SQL injection problem? And what is the user input? (2) What is the final SQL statement will be? SELECT FROM employee WHERE username-‘sha256(SuName)’ Show transcribed image text Suppose the private key file for S1 is object O1, and only S1 can read. Suppose the public key file for S1 is object 02, and all can read, but only S1 can write. Suppose all can read and write from object 03. Please complete the following access matrix. 03 02 01 S1 S2 S3
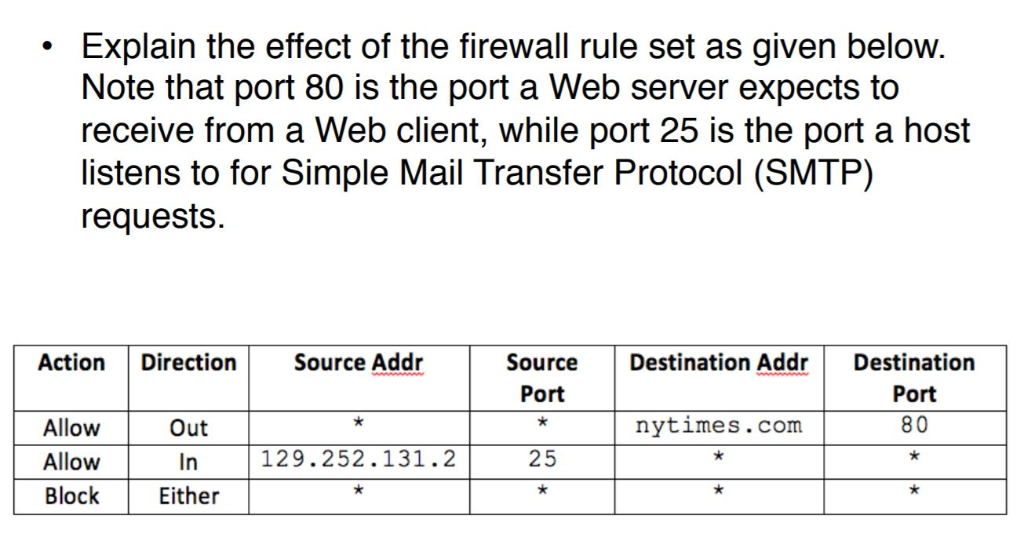
Explain the effect of the firewall rule set as given below Note that port 80 is the port a Web server expects to receive from a Web client, while port 25 is the port a host listens to for Simple Mail Transfer Protocol (SMTP) requests. SourceDestination Addr Destination Action Direction Source Addr Port Port 80 nytimes.com Allow Allow Block Out In Either 129.252.131.2 25
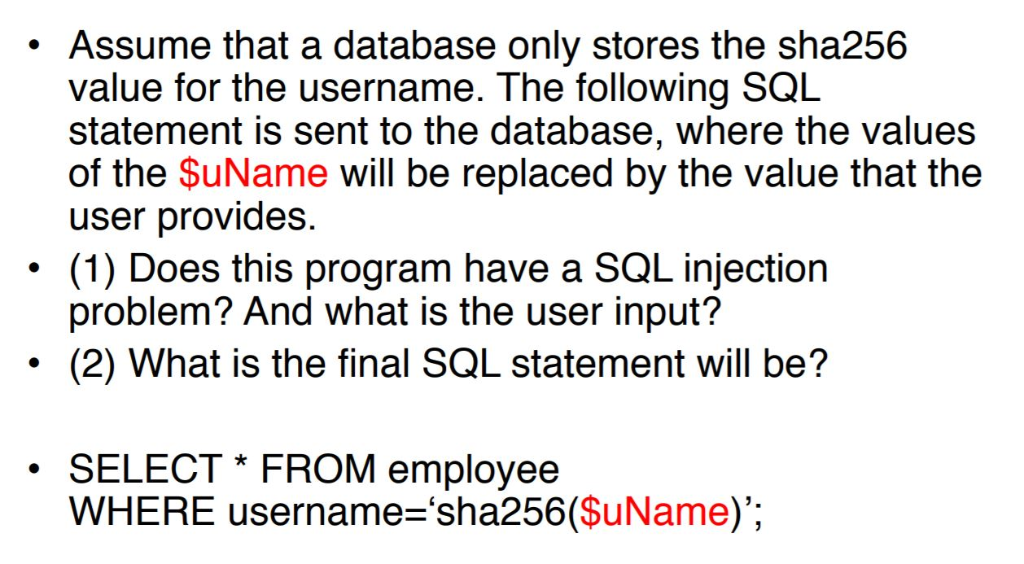
. Assume that a database only stores the sha256 value for the username. The following SQL statement is sent to the database, where the values of the $uName will be replaced by the value that the user provides . (1) Does this program have a SQL injection problem? And what is the user input? (2) What is the final SQL statement will be? SELECT FROM employee WHERE username-‘sha256(SuName)’
Expert Answer
Answer to Can someone help me with some questions please 1. 2. 4. … . . .
OR

